TLDR
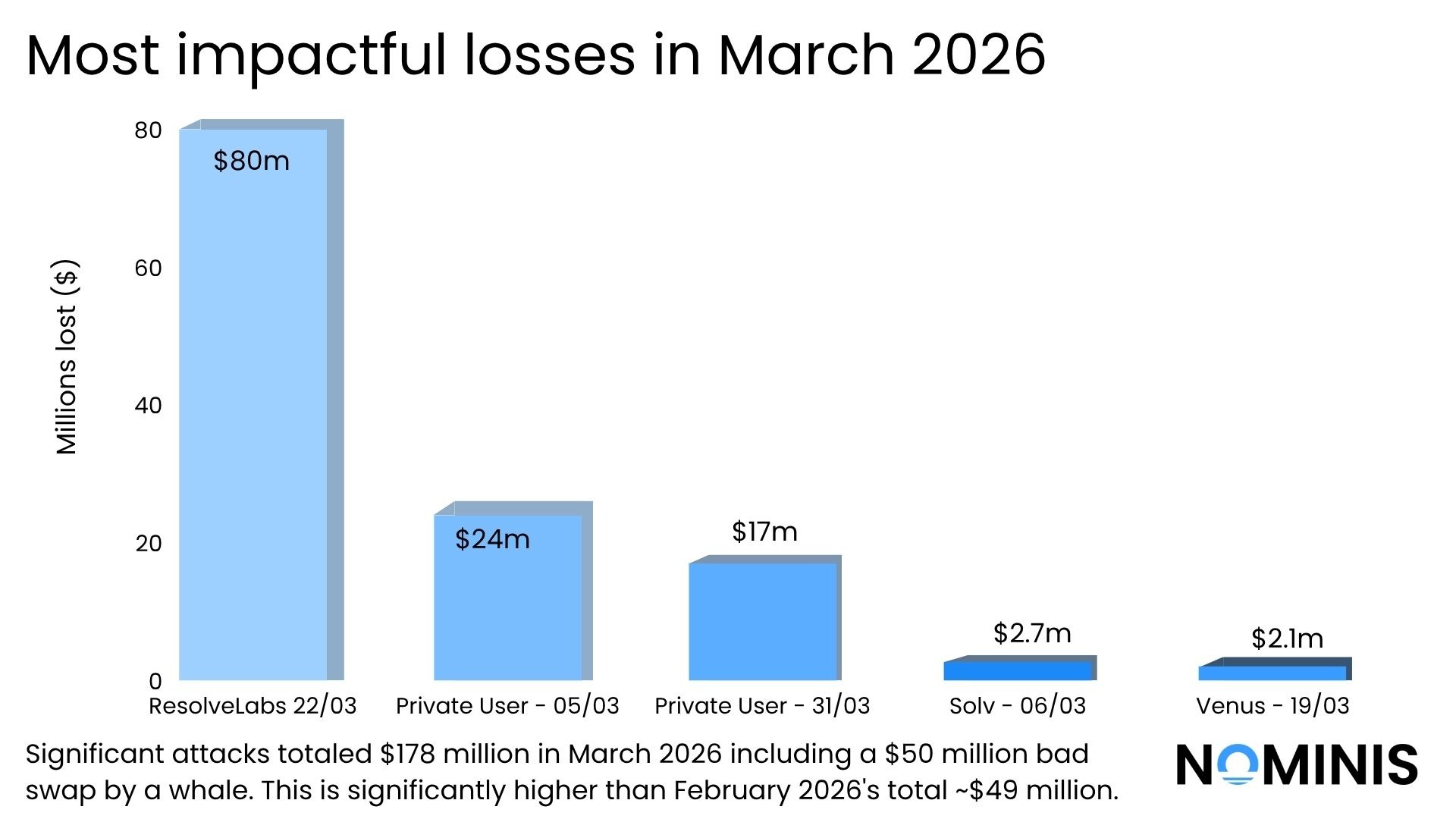
- Approximately $178.1 million was lost across major crypto incidents in March 2026, representing a sharp increase compared to February’s ~$49.3 million, largely driven by several high-impact events including a stablecoin minting exploit and a major user compromise.
- A single protocol-level failure at Resolv Labs, which resulted in approximately $80 million in losses due to unbacked stablecoin minting, accounted for a significant share of total losses and highlighted the systemic risk posed by failures in core financial logic.
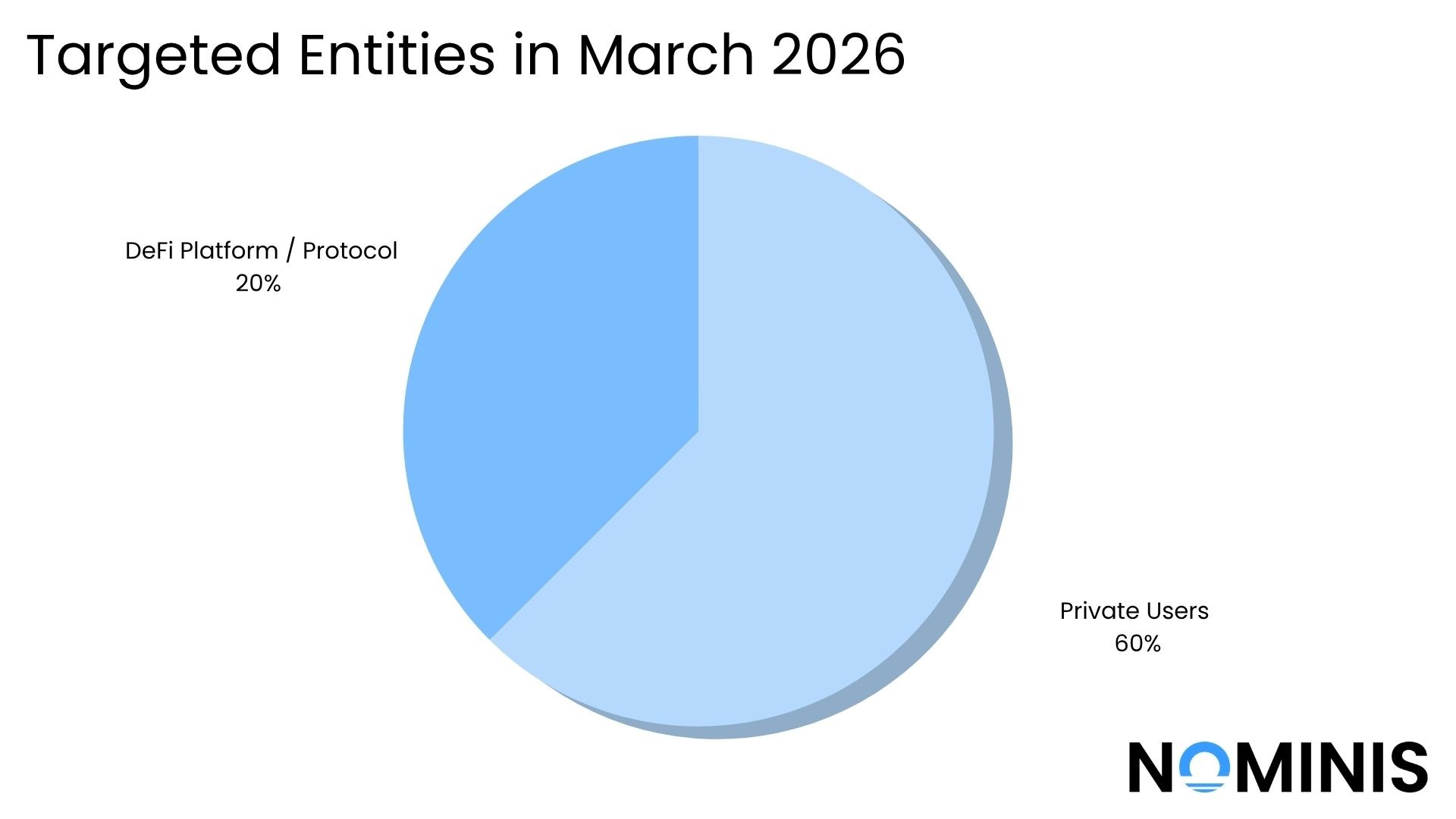
- Private individuals remained the most frequently targeted victims, accounting for the majority of incidents, with attackers primarily relying on phishing techniques, malicious permit signatures, and social engineering rather than exploiting technical vulnerabilities.
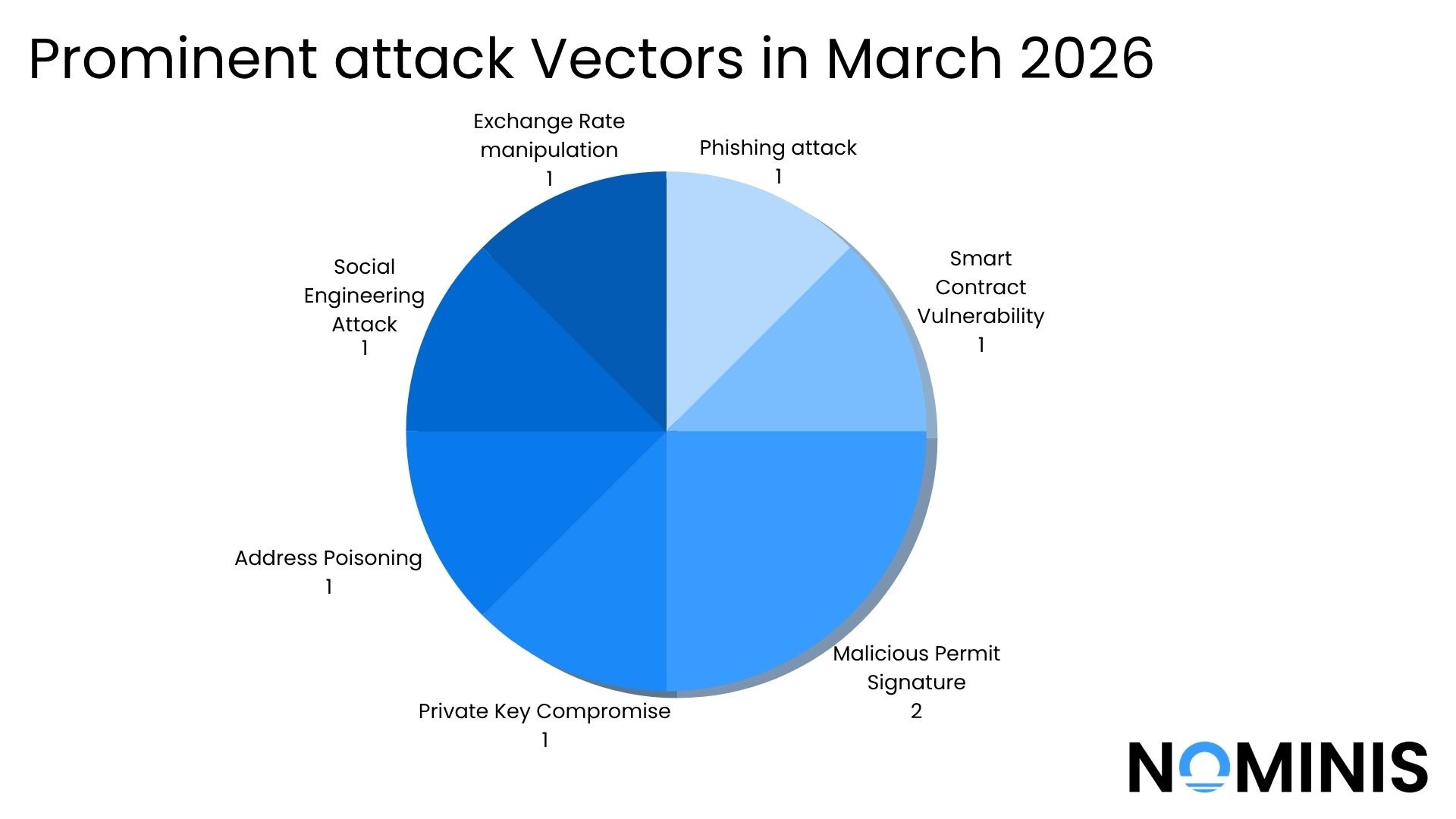
- Authorisation abuse continued to dominate as the primary attack vector, with multiple incidents involving victims unknowingly approving transactions that granted attackers direct access to their funds. These attacks enabled rapid draining of assets without requiring private key compromise.
- Across the month, social engineering and interaction-based exploits caused more cumulative damage than smart contract vulnerabilities, reinforcing the ongoing shift toward attacks that exploit user behaviour and trust rather than code-level weaknesses.
- While DeFi protocol exploits did occur, including incidents affecting lending and vault mechanisms, these were typically linked to design and logic flaws, such as pricing manipulation and collateral miscalculations, rather than traditional bugs.
- Stablecoins played a central role in March’s incidents, both as primary targets in wallet-draining attacks and as points of systemic failure, as demonstrated by the collapse of USR following the minting exploit.
- Cross-chain activity and fund fragmentation were consistently observed in post-exploit behaviour, with attackers leveraging bridges and multiple wallets to obscure transaction trails and delay detection.
Introduction
March 2026 marked a significant escalation in both the scale and complexity of crypto-related risk, with total losses rising sharply compared to the previous month. The incidents observed throughout the period reflect a maturing threat landscape, where attackers increasingly target not only technical vulnerabilities, but also user behaviour, protocol design, and the broader infrastructure underpinning the ecosystem.
This report provides a comprehensive overview of the most impactful incidents, emerging attack patterns, and structural risks identified during the month. It examines both user-level compromises and protocol-level failures, alongside wider ecosystem events and NOMINIS’ proprietary research into sanctions evasion, compliance challenges, and evolving financial networks.
A key theme throughout March is the growing importance of trust layers, the points at which users, protocols, and infrastructure interact. Whether through malicious transaction approvals, flawed financial logic, or indirect exposure within complex systems, many of the most significant incidents did not rely on traditional exploits, but instead leveraged weaknesses in how crypto systems are designed and used.
As the ecosystem continues to scale and interconnect, understanding these risks requires moving beyond isolated events and toward a system-level perspective. This report aims to provide that context, offering both detailed incident analysis and broader insights into the evolving nature of crypto security and financial crime.
Major Crypto attacks in March 2026
Private User - 05/03/2026
Type: Address Poisoning Attack
To begin the month, a private user owning a wallet linked to ‘Silly Tuna’ experienced a targeted address poisoning attack, where the victim likely copied a spoofed address (with matching prefix/suffix) from their transaction history and inadvertently transferred funds to the attacker. The compromised wallet associated with “sillytuna” was drained of approximately $24M in aEthUSDC. After the exploit, the attacker swapped a significant portion into DAI to reduce volatility of the coin, consolidating ~$20M across two staging addresses, suggesting preparation for further obfuscation. The subsequent bridging of smaller tranches to Arbitrum indicates early-stage laundering via cross-chain fragmentation, which is a common tactic to further complicate on chain tracing or delay any kind of detection.
Impact: $24,000,000
Solv Protocol - 05/03/2026
Type: Contract Vulnerability
The following day, Solv Protocol, a decentralised finance protocol, experienced a loss when a vulnerability in one of its vault smart contracts on BNB chain allowed an attacker to manipulate internal accounting or pricing logic, and withdraw more assets than they were entitled to. $2.7 million worth of SolvBTC, a Bitcoin pegged token, was drained as a result. Post incident, the team confirmed the incident was contained to a specific ault rather than the entire protocol, and the team responded by pausing affected components and beginning an investigation.
Impact: $2,700,000
Private User - 17/03/2026
Type: Malicious Permit Address
In the middle of March, a Private User experienced a phishing-based approval exploit in which they lost approximately $280k in USDC and USDT, after signing a malicious permit transaction. By approving the signature, the victim, wallet address 0xB2… ,unknowingly granted the attacker permission to transfer tokens directly from their wallet without requiring further interaction. The attacker then used multiple phishing-controlled addresses to execute the drain and disperse funds, a common tactic to reduce traceability. This type of attack does not involve a smart contract vulnerability but instead exploits user-side signing behavior, where deceptive interfaces or links trick users into authorizing token allowances that can be immediately abused. This is a classic example of an exploit taking advantage of human trust, as opposed to a technical hack.
Impact: $280,000
Private User - 17/03/2026
Type: Phishing
On the same day, another private user also suffered a phishing-based approval exploit on Ethereum, losing approximately $1.77 million in USDC after signing a malicious permit signature. The victim, wallet address 0x05…, unknowingly granted the attacker permission to transfer funds directly from their wallet without requiring an on-chain transaction from the victim. On-chain behaviour suggests the attacker appeared to use multiple controlled addresses to execute the drain and distribute stolen funds, which is a common obfuscation technique discussed earlier to reduce traceability.
Impact: $1,770,000
Thena of Venus - 19/03/2026
Type: Exchange Rate Manipulation
Several days, Venus Protocol, a decentralised finance lending and borrowing protocol experienced a smart contract-level exploit on the BNB chain, in which an attacker manipulated the protocol’s borrowing logic to extract excess funds. By exploiting a flaw in how collateral values and borrowing limits were calculated, the attacker was able to take out undercollateralised loans and leave the protocol with approximately $2.18 million in bad debt. The exploit stemmed from a weakness in the protocol’s on-chain logic, which allowed the attacker to systematically withdraw funds beyond what should have been permitted.
Impact: $2,180,000
Private User - 20/03/2026
Type: Malicious Permit Address
In mid March, an additional private user experienced a phishing-based approval exploit on Ethereum, in which a user lost approximately $200k in USDC and wmtUSDT after signing malicious Permit and Approve transactions. These signatures granted the attacker spending allowances over the victim’s tokens, enabling them to transfer funds directly from the wallet without further consent. The attacker then executed the drain using multiple phishing-controlled addresses, a common tactic to distribute and obscure stolen assets.
Impact: $200,000
ResolveLabs - 22/03/2026
Type: Private Key Compromise
Days later an incident was detected involving Resolv Labs, a decentralised finance protocol. A minting logic exploit allowed an attacker to create approximately $80 million worth of unbacked USR. Due to a flaw in the completeSwap() function, the protocol failed to properly validate collateral inputs, enabling the attacker to deposit only ~$100K–$200K and mint vastly more tokens, a severe breakdown in the collateralization model. This artificial supply inflation immediately destabilized the system, causing USR to lose its peg and crash by roughly 74% as liquidity rapidly exited pools. The attacker has since begun swapping a portion of the minted tokens into Ethereum-based assets like ETH and distributing funds across multiple wallets, indicating active laundering. Unlike typical exploits that drain reserves, this attack undermined the core backing mechanism itself; an example of how stablecoins can collapse abruptly when issuance controls fail.
Impact: $80,000,000
Private User - 31/03/2026
Type: Social Engineering Attack
On the last day of March, an incident was reported involving a social engineering attack on a Kraken user, who had accumulated about 8,662 ETH, worth about $18 million. The attacker gained unauthorized access to the victim’s account or credentials, likely through deception rather than a technical exploit, and proceeded to move funds. Approximately $1.7M in ETH was bridged via THORChain, a step commonly used to obscure transaction trails, before being deposited into HitBTC. In addition, a much larger portion, 5,347.9 ETH, was transferred directly to the same exchange.
Impact: $17,000,000
Significant Events in March 2026
March 2026 saw a series of high-impact security incidents across both DeFi and Web2 infrastructure, highlighting persistent weaknesses in user interaction layers, protocol design, and software supply chains.
One notable incident flagged by SlowMist involved a phishing-based attack in which users were tricked into signing malicious transactions, granting attackers token spending approvals. These exploits did not rely on smart contract vulnerabilities but instead abused permit and approval mechanisms, enabling attackers to drain funds directly from user wallets once authorization was given, underscoring the growing threat of social engineering in crypto.
At the protocol level, concerns around systemic risk in DeFi were further highlighted by commentary on X, following an incident in which a user attempted to swap $50M in USDT for AAVE through the Aave interface. Despite clear warnings about extreme slippage, explicitly acknowledged by the user, the transaction executed under expected market conditions, ultimately resulting in a highly unfavorable outcome of just 324 AAVE. While the underlying infrastructure and routing mechanisms functioned as designed, the event underscores a broader issue in DeFi: permissionless systems can still produce materially adverse outcomes even without bugs or exploits. The scale of the trade amplified its impact, exposing limitations in liquidity depth, execution safeguards, and user protection mechanisms. This incident reinforces the need for improved guardrails at the interface and protocol design level, particularly as transaction sizes and institutional participation in DeFi continue to grow.
Beyond DeFi, the ecosystem was also affected by a major supply chain compromise involving Axios, as detailed by Halborn. Attackers briefly gained control of the package distribution process and published malicious versions containing hidden malware. Although the exposure window was short, the scale of Axios usage meant the potential impact was significant, demonstrating how trusted developer dependencies can become attack vectors.
Together, these incidents illustrate a key theme for March 2026: attackers are increasingly targeting trust layers, whether through user signatures, protocol assumptions, or widely used software packages, rather than relying solely on traditional exploits.
NOMINIS Unique Findings
Sanctions Evasion and State-Linked Financial Networks
NOMINIS’ research throughout March 2026 highlights the increasing complexity of illicit finance, with a particular focus on how sanctions evasion and state-linked financial activity are evolving across both traditional and crypto infrastructure. Analysis of UAE–Iran financial relations, alongside multiple reports on Iranian Revolutionary Guard Corps (IRGC)-linked activity, in the UK, linked to both attacks on British bases in the Gulf, and terror activity in London, demonstrates how cross-border financial corridors enable sanctioned entities to maintain access to global markets. These flows are rarely direct; instead, they rely on layered systems involving intermediaries, trade relationships, and blockchain-based infrastructure. Notably, UK-based banks and crypto services were identified as being indirectly exposed to these flows, underscoring a critical risk: institutions can remain compliant at an individual level while still facilitating illicit activity as part of a broader transactional network. This reflects a shift toward sanctions evasion as a systemic, infrastructure-driven challenge rather than one confined to identifiable bad actors.
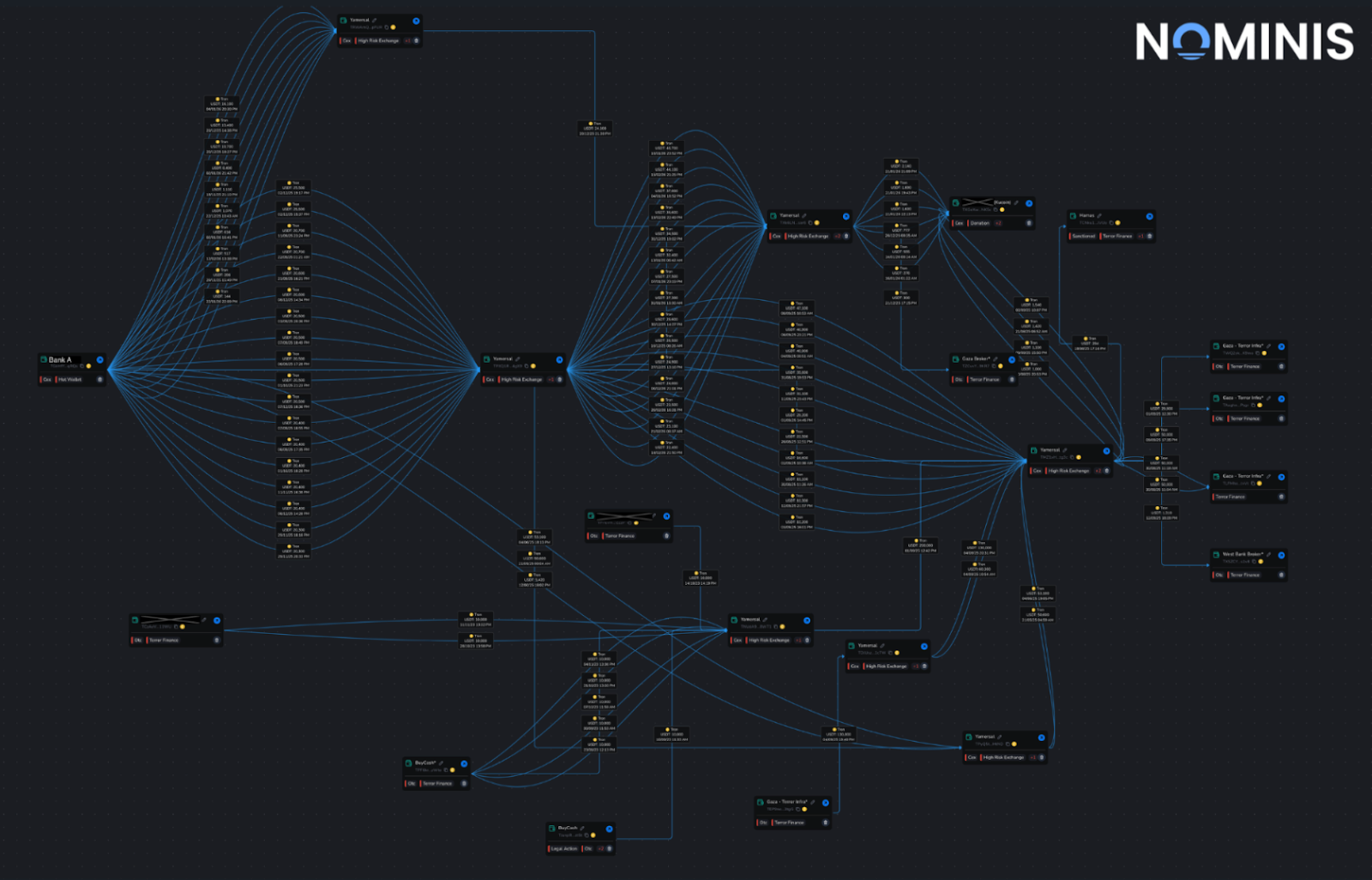
Enforcement, Anti Money-Laundering, and Counter-Terror Financing
At the same time, enforcement actions targeting illicit finance are becoming more visible but remain inherently reactive. Cases such as the UK’s crackdown on Xinbi illicit marketplace and the NBCTF seizure of Hamas-linked wallets illustrate growing capabilities among authorities to identify and disrupt illicit networks. However, these actions typically occur only after networks have already scaled, limiting their preventative impact. Illicit actors continue to demonstrate a high degree of adaptability, rapidly moving funds across wallets, chains, and jurisdictions to evade detection. As a result, while enforcement is improving, it still struggles to match the speed and flexibility of the underlying financial activity.
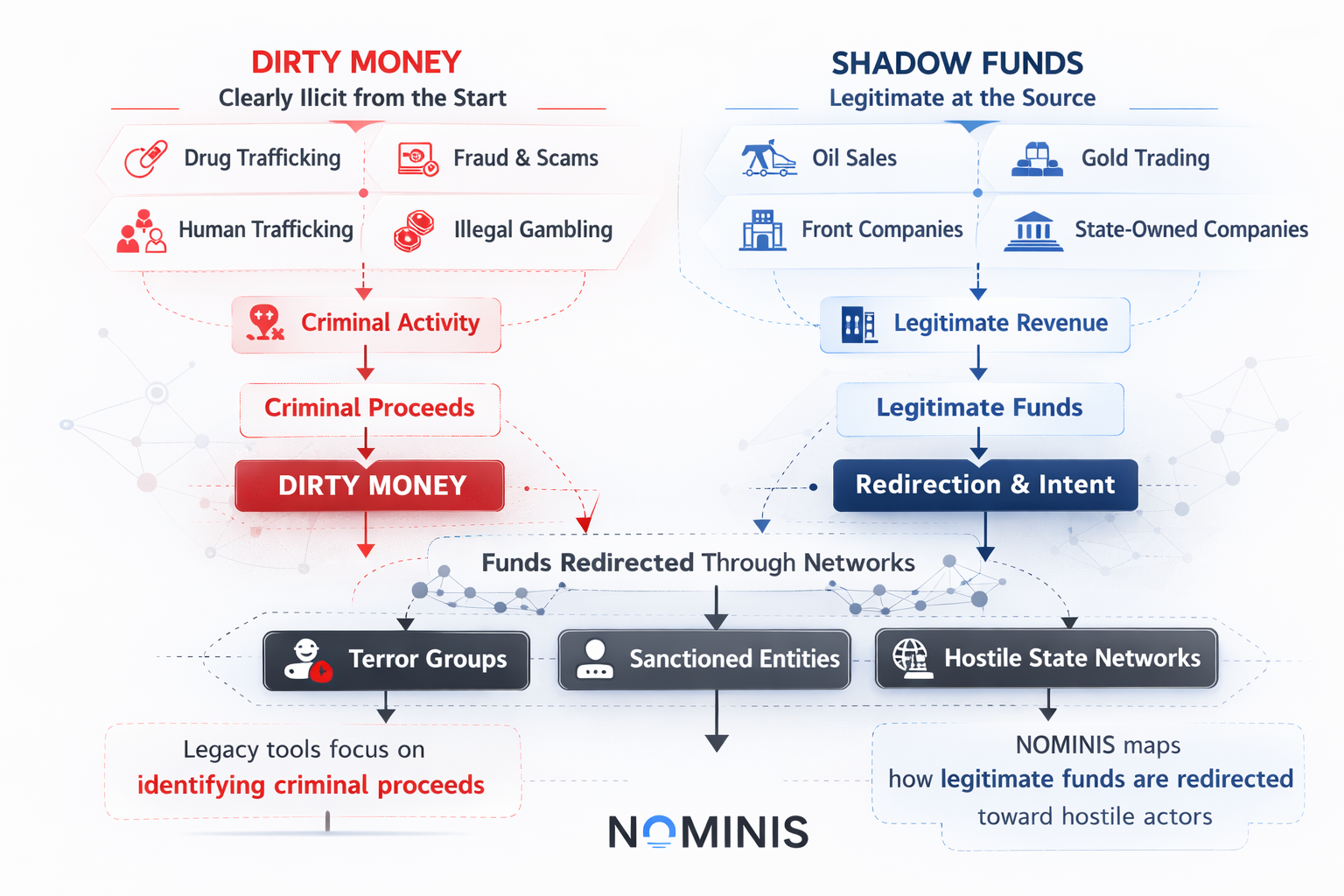
Compliance Operations and Structural Weaknesses
NOMINIS also highlights persistent structural weaknesses in compliance operations. The analysis of no-KYC exchanges reveals how these platforms leverage nested infrastructure, indirect access to regulated services, to bypass traditional controls. This is compounded by broader challenges in how financial risk is defined and managed. The distinction between “dirty money” and “shadow funds” is particularly important, as it reflects the growing prevalence of legally ambiguous flows tied to sanctions exposure rather than outright criminality. Existing AML and CFT frameworks, which are often designed to detect illicit activity, are not well equipped to address these grey areas. Common operational shortcomings, including over-reliance on static wallet screening and insufficient network-level analysis, further limit the effectiveness of compliance systems in identifying indirect exposure.
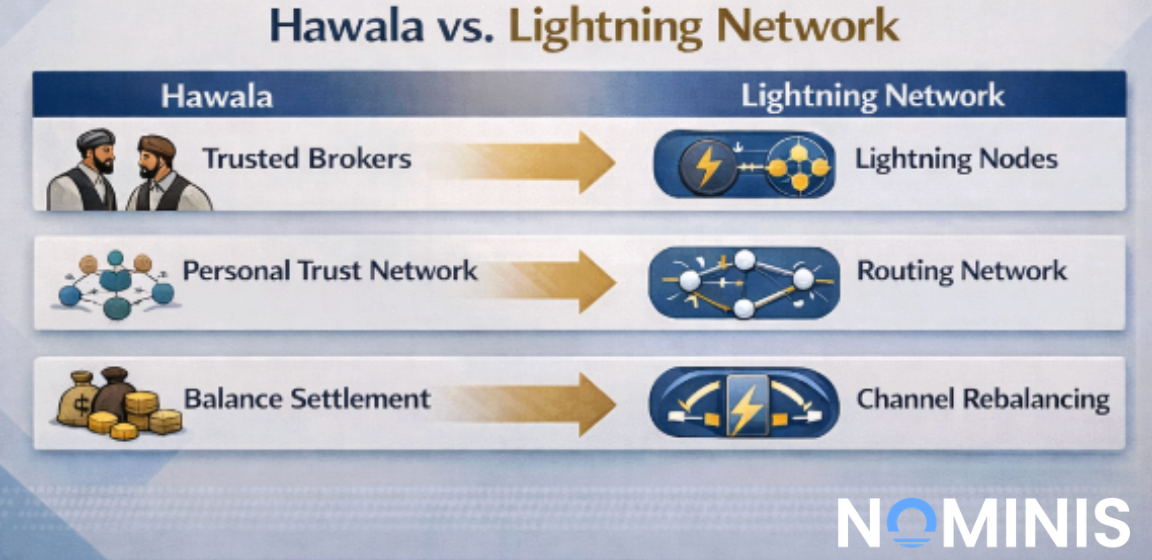
Alternative Financial Systems and the Evolution of Crypto
Finally, NOMINIS’ exploration of crypto in relation to Hawala systems provides important context for understanding how financial networks are evolving. Rather than replacing traditional informal systems, crypto is increasingly integrating with them, creating hybrid models that combine on-chain transactions with off-chain coordination and trust-based relationships. This convergence further complicates oversight, as financial activity becomes more distributed and less dependent on any single system or jurisdiction.
Taken together, these insights point to a broader transformation in financial crime. The central challenge is no longer simply identifying illicit actors, but understanding and managing exposure within complex, interconnected systems. As financial networks become more layered and adaptive, risk is increasingly defined by participation in these systems, whether direct or indirect, requiring a fundamental shift in how compliance, enforcement, and risk assessment are approached.
NOMINIS Updates
Following last month’s release of the NOMINIS Forensic Tool, March 2026 marks the introduction of AsKYT, a Bitcoin-focused GPT designed for investigators and compliance teams to query wallet and transaction data against the NOMINIS database. Built around the goal of making complex on-chain investigations both efficient and reliable, AskYT enables users to ask natural-language questions about Bitcoin wallets, transactions, and activity, and receive structured, explainable insights grounded in on-chain data. The tool is designed to support both high-level exploration and more targeted investigative workflows, combining ease of use with the analytical depth required for professional use. By reducing friction without compromising data integrity, AskYT reflects a broader shift toward more accessible yet rigorous blockchain intelligence tools. To receive access to AsKYT, email contact@nominis.io.
Conclusion:
March 2026 highlighted both the scale and evolving nature of risk across the crypto ecosystem, with total losses reaching approximately $178.1 million, including a significant portion driven by a single high-impact event involving the AAVE swap incident. Activity spanned multiple chains, primarily Ethereum, alongside BNB Chain and THORChain, and involved a wide range of assets, from stablecoins such as USDC and USDT to more complex instruments like SolvBTC and USR.
A clear pattern emerged in the types of targets and attack vectors observed. The majority of incidents affected private users, with exploits largely driven by phishing, social engineering, and malicious approval signatures rather than technical vulnerabilities. At the same time, several DeFi protocols were impacted by smart contract flaws and design weaknesses, including pricing manipulation and minting logic failures. Notably, the most severe protocol-level incident, the Resolv Labs exploit, demonstrated how failures in core financial logic, particularly around stablecoin issuance, can lead to immediate and systemic breakdowns.
Across both user-level and protocol-level incidents, attackers consistently leveraged trust-based weaknesses. Whether through deceptive interfaces, permissionless transaction execution, or flawed protocol assumptions, exploits increasingly targeted the layers where users and systems interact, rather than relying solely on code-level bugs. This trend was further reinforced by broader ecosystem events, including supply chain compromises and high-risk transaction execution scenarios, which exposed limitations in both user safeguards and infrastructure design.
NOMINIS’ research complements these findings by emphasizing that risk is no longer isolated to individual actors or events, but is embedded within complex, interconnected financial systems. Sanctions evasion, indirect exposure, and hybrid financial networks combining traditional and on-chain elements all point to a structural shift in how illicit activity operates. While enforcement actions and compliance frameworks continue to evolve, they remain largely reactive and are challenged by the speed and adaptability of these systems.
Observed together, March 2026 underscores a critical transition: the primary threat is no longer just technical exploitation, but systemic risk arising from trust, connectivity, and scale. Addressing this will require not only stronger technical defenses, but also improved user protections, more robust protocol design, and a shift toward network-level risk analysis across the industry.
All research content and accompanying reports are provided for informational purposes only and should not be relied upon as professional advice. Accessing these materials does not create any professional relationship or duty of care. Readers are encouraged to consult appropriately qualified professionals for guidance. We uphold the highest standards of accuracy in all the information we provide. For any questions or feedback, please contact us at contact@nominis.io.



.jpg)


