Crypto compliance has matured rapidly over the past 5 years, but many AML/ CTF leaders are still operating within frameworks built for an earlier stage of the industry.
Transaction volumes have increased, geopolitical tensions can intensified, and stablecoins have become embedded in global trade. Meanwhile, compliance methodologies, and adoption of more suitable strategies, have failed to maintain an equal pace.
Across the market, we continue to see several recurring mistakes:
- An overfocus on confirmed illicit funds while neglecting nuanced spectrum of shadow funds;
- False confidence in ‘safe’ jurisdictions
- Binary risk methodologies applied arbitrarily to a complex financial network
- Excessive (and therefore wasteful) consumption of unnecessary, irrelevant data assuming traditional AML methodologies apply to a variety of use cases
- And the underuse of off-chain intelligence data attribution.
Each of these weaken a compliance program, leaving blind spots, and together, render institutions, payment providers and VASPs with systemic weaknesses that sophisticated actors increasingly exploit.
- Focusing Only on Confirmed Dirty Money, while neglecting the nuanced spectrum of Shadow Funds
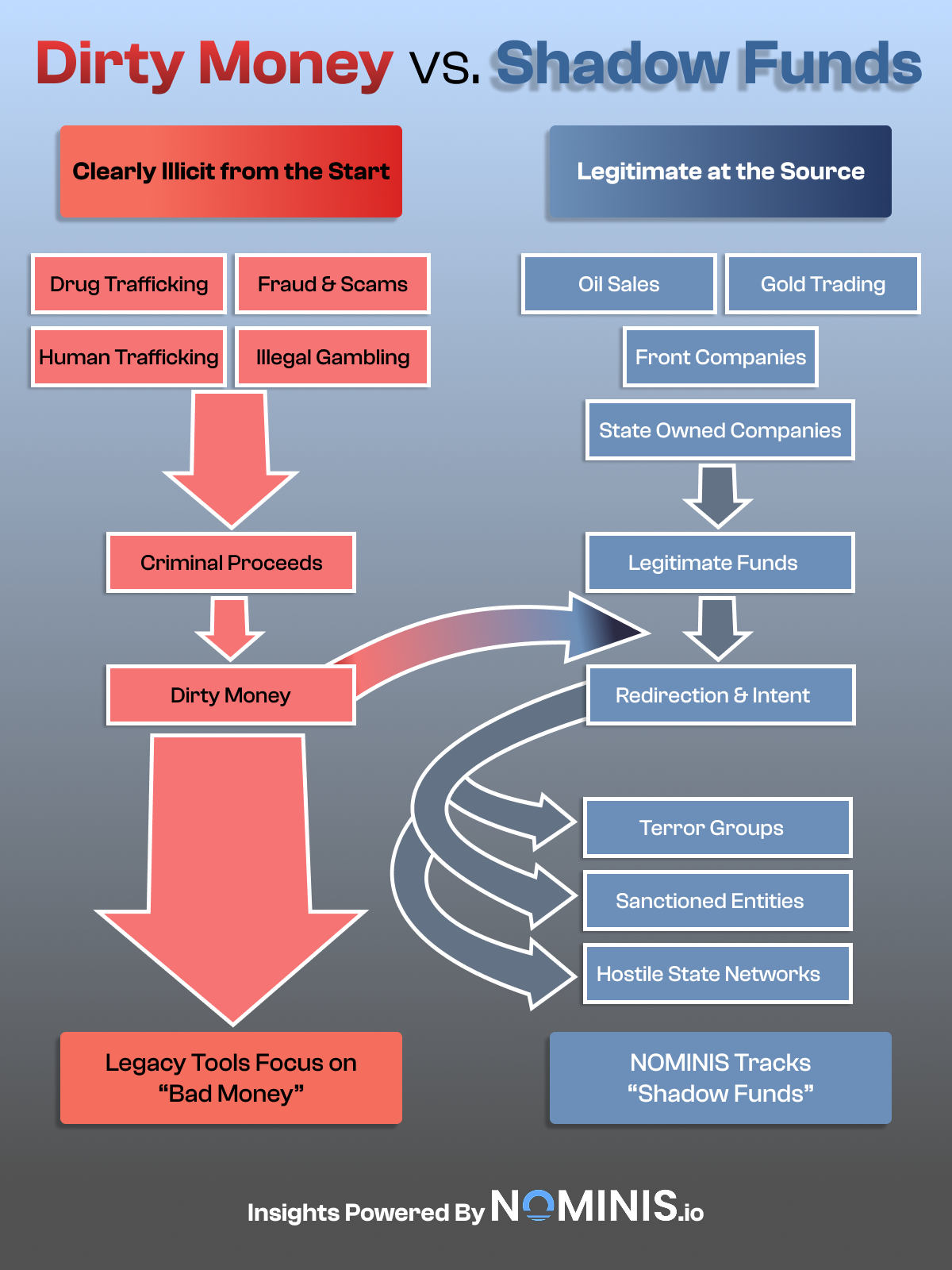
Traditional AML frameworks were designed to detect proceeds of crime. Drug Trafficking, ransomware, fraud, human trafficking, organised crime and illegal gambling all produce clearly illicit funds. These flows are easier to categorise, easier to label, and easier to explain to regulators when they knock.
However, NOMINIS is increasingly recognizing that modern terror financing and hostile state funding frequently do not begin as criminal proceeds. They often originate from entirely legitimate activities: oil sales, gold trading, state-linked enterprises, front companies, or even charitable donations. The funds themselves are not inherently illegal at origin, but the risk emerges later, when those funds are strategically redirected to sanctioned groups, terror organisations, or hostile state networks.
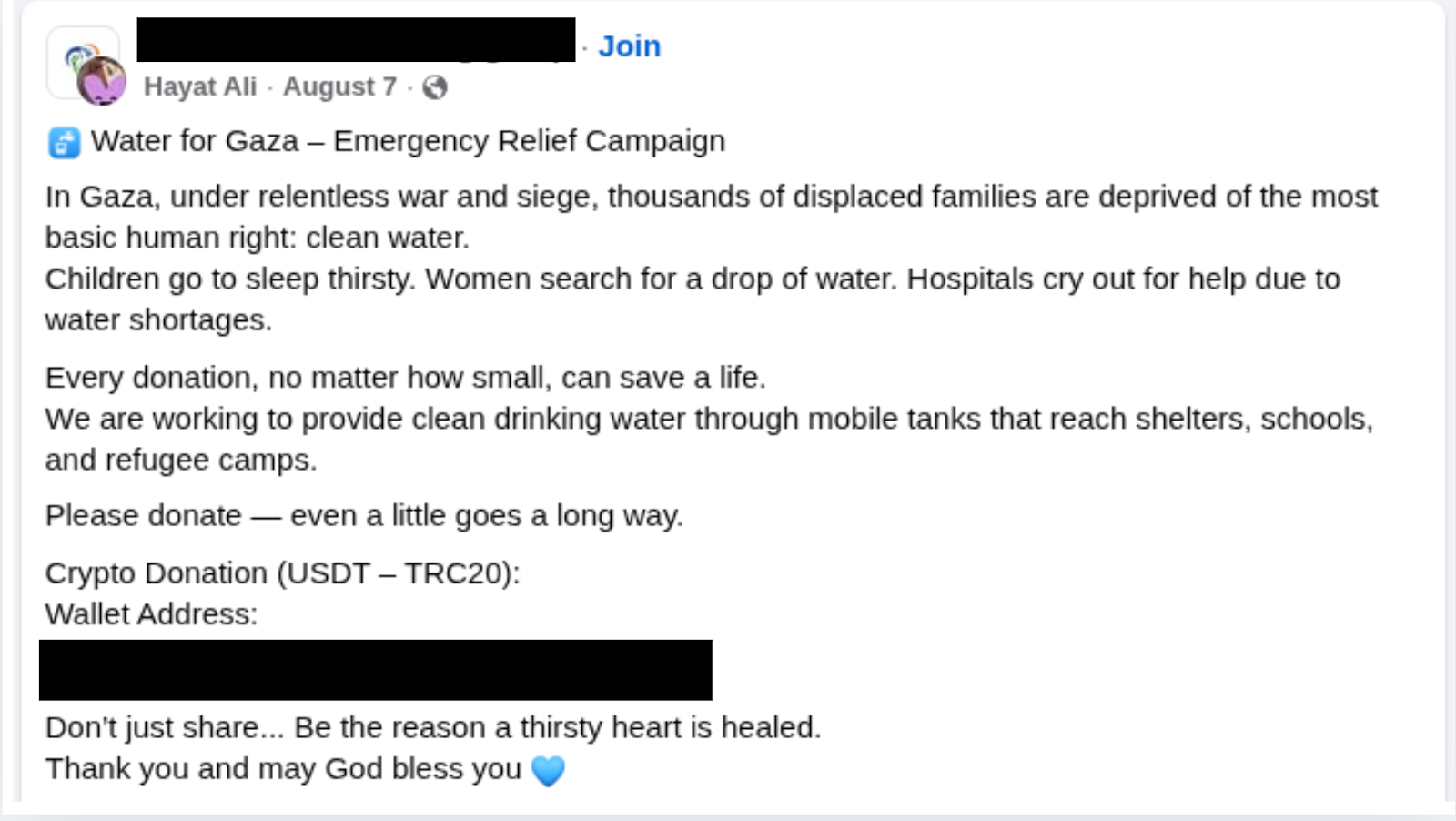
The above social media post demonstrates an attempt to raise crypto donations for a humanitarian cause. Unfortunately, the wallet address given in the social media post belongs to designated terror group Hamas, who have been known to use such humanitarian branding to solicit funds and redirect them into terror funding networks.
This would be the difference between dirty money and shadow funds. Dirty money is criminal at the source, but shadow funds are legitimate at source; they eventually become weaponised through intent, and redirection.
Many legacy compliance tools are built to detect known bad actors and previously identified criminal typologies. They perform far less effectively when dealing with capital that sits in legal grey zones before being strategically deployed. When screening programs focus exclusively on officially classified bad money, they miss the financial infrastructure that supports far more sophisticated threats.
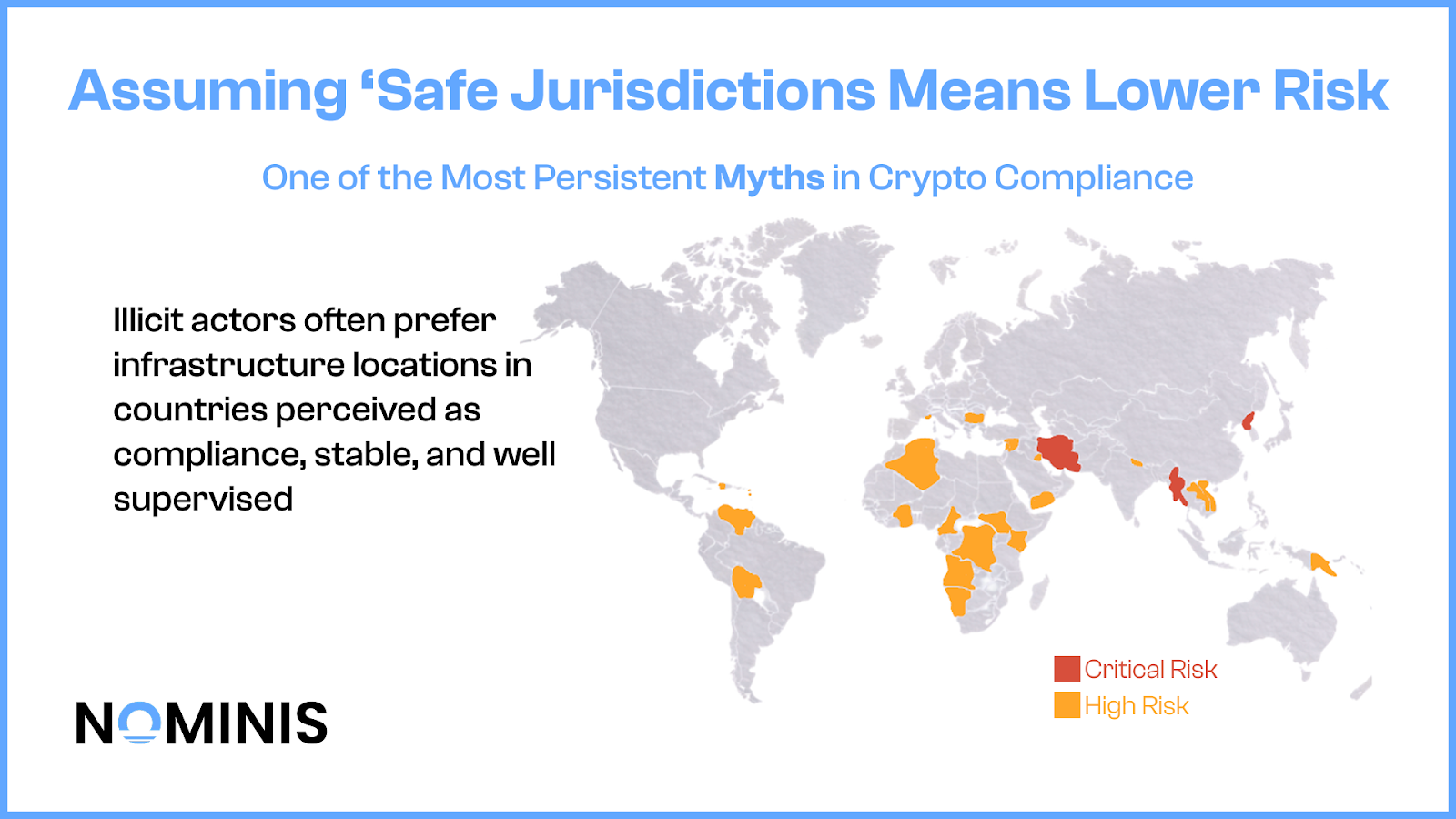
2. Assuming safe Jurisdictions mean lower risk
One of the most persistent myths in crypto compliance is that operations in a jurisdiction considered safe by the Financial Action Task Force, such as the US, UK and Canada, significantly reduces exposure to high-risk actors. Internal risk models often reflect this assumption, assigning lower inherent risk to exchanges based in London or other ‘low risk’ countries.
However, new evidence suggests the complete opposite.
Recent NOMINIS analysis found that illicit actors are twelve times more likely to use exchanges in low risk FATF jurisdictions, than high risk ones. The logic is as follows; well-regulated environments have liquidity, banking access, reputational legitimacy, and importantly, a perception of safety, that can be manipulated by illicit actors and terrorists.
Via clustering analysis, backend wallet attribution, and infrastructure mapping, NOMINIS revealed that infrastructure linked to the Islamic Revolutionary Guard Corps (IRGC) moved millions through London-based exchanges, including Zedcex Zedxion. These exchanges operated within a respected financial jurisdiction, yet were embedded in laundering networks tied to a designated terror entity.
These findings demonstrate that actors seeking to move funds discreetly do not gravitate toward already-sanctioned environments. They prefer infrastructure located in countries perceived as compliant, stable, and well-supervised. That perception lowers scrutiny from counterparties and increases the likelihood that transactions will pass initial risk filters. Compliance leaders who rely too heavily on geographic comfort risks overlooking the very environments that sophisticated networks deliberately exploit.
3. Using Binary Methodologies for a nuanced Risk spectrum
Many compliance programs still rely heavily on boolean logic; a wallet is either associated with a sanctioned wallet, or not and an address is either flagged, or not.
This approach may work reasonably well when dealing with clearly identified criminal actors, but it simply cannot be used for shadow funds.
Shadow fund networks often exist within partial associations, indirect exposure, or layered transactional chains. A wallet may not be directly sanctioned, but may cluster with infrastructure tied to state-linked entities. Funds may pass through commodities, fiat rails, OTC brokers, and stablecoins, before reaching their final destination. None of these steps individually trigger a definitive red flag, yet collectively, they indicate strategic financial coordination.
A binary compliance policy framework struggles to capture the nuance. Complex intelligence issues are reduced into checkbox exercises, meanwhile, effective shadow funds analysis require granularity, infrastructure mapping, clustering analysis and contextual intelligence layering. Without such depth, risk scoring systems underestimate exposure and compliance teams are left with an incomplete picture.
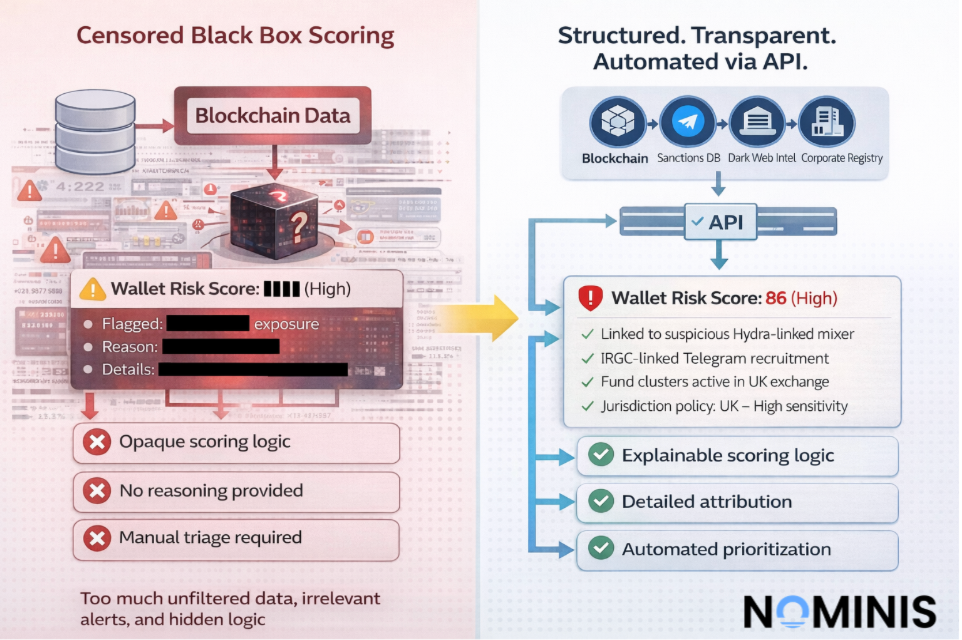
4. Assuming more data necessarily improves quality of your Intelligence Findings
Sometimes less actually is more. One of the most persistent misconceptions in crypto compliance is the belief that more data and more tools will naturally result in stronger intelligence. In practice, accumulation does not necessarily produce clarity, and the expansion of datasets often introduces complexity that outweighs any incremental benefit.
Many organisations subscribe to multiple overlapping sanctions feeds, risk databases, blockchain analytics platforms, and transaction monitoring systems under the assumption that broader coverage strengthens oversight. As additional dashboards and alert systems are layered into the workflow, alert volumes increase, interfaces multiply, and operational pressure intensifies, yet the overall quality of insight does not proportionally improve. When intelligence remains confined within user interfaces rather than accessible through full APIs, companies cannot truly own or operationalise their data. Without structured access, they are unable to train internal machine learning models, refine decision-making logic, or build proprietary risk frameworks. The value remains trapped in the tool, rather than compounding inside the organisation.
Raw blockchain data without structured intelligence can slow investigations rather than strengthen them, particularly when compliance teams focus narrowly on on-chain behaviour while the predicate crime is unfolding in the real world. Financial flows may be visible on-chain, but intent, coordination, recruitment, and commercial activity frequently occur across the open web, deep web, and dark web. Monitoring and attributing these environments to blockchain activity is essential for contextual accuracy. Without this broader intelligence layer, analysis risks becoming technically precise but strategically incomplete.
Excessive and uncurated interfaces also create noise and alert fatigue, gradually desensitising analysts to genuinely meaningful signals. When large portions of activity are flagged without clear prioritisation, urgency becomes diluted and strategic threats can remain obscured beneath layers of low-value alerts. The problem is compounded when uniform risk policies are applied across materially different jurisdictions. Sensitivities surrounding gambling exposure in Dubai, for example, differ significantly from those in Malta, yet many organisations rely on static frameworks that fail to reflect local regulatory nuance or commercial reality.
In response to mounting complexity, some organisations add manual forensic tools in the belief that deeper technical capability will automatically strengthen compliance. In reality, much of the underlying data remains underutilised, while overlapping datasets and redundant features increase cost without meaningfully improving investigative precision. Rather than enhancing detection, fragmentation can weaken it by scattering intelligence across disconnected systems and preventing cohesive model development.
What effective compliance programs require is not maximal data acquisition, but purposeful intelligence architecture. This means owning structured data through API access, integrating on-chain and off-chain intelligence, calibrating jurisdiction-specific risk frameworks, and embedding compliance into strategic decision-making. When intelligence is explainable, adaptable, and operationalized internally, compliance shifts from being a defensive cost centre to becoming a growth enabler that strengthens trust, accelerates partnerships, and supports sustainable expansion.
5. Underestimating the Value of Off-Chain Intelligence Attribution
Blockchain transparency is powerful, but incomplete. On-chain data shows movement of funds, timestamps, and wallet relationships, but does not reveal intention, ownership, strategic coordination, or common network.
Sophisticated networks combine on-chain activity with off-chain mechanisms such as OTC brokers, shell companies, messaging platforms, commodity trades, and informal value transfer systems. Without incorporating off-chain intelligence, compliance teams may see transactions, but entirely miss the broader structure.
Open-source intelligence, Dark-web monitoring, GeoIntelligence and other sources of intelligence often provide the context necessary to interpret blockchain behavior accurately, and ensure a sensible, all-encompassing risk screening score. Wallets that appear benign on chain, can take on entirely different risk scores when off-chain signals are read.
Relying solely on blockchain data created a fragmented view of risk. Modern compliance requires layered intelligence that connects digital transactions to real-world actors and infrastructure.
What The Strategic Shift to Crypto Means for AML/ CFT Leaders
AML traditionally focuses on criminal proceeds, but CFT increasingly requires understanding how legitimate capital is redirected for strategic harm.
As stablecoins become embedded in global financial flows and geopolitical tensions intensify, shadow funds are becoming both more scalable and harder to quantify than traditional dirty money. They move through commodity trades, enterprises, front businesses and OTC channels before even touching the blockchain. By the time they appear on-chain, they’ll appear benign. The risk is not visible in the origin of funds, but in the architecture that guides them.
Compliance leaders who continue to focus narrowly on classified bad actors, rely on jurisdictional assumptions, apply binary methodologies, overconsume unstructured data, and neglect off-chain intelligence are not failing because they lack tools. They are failing because they are solving yesterday’s problem.
Crypto Compliance is moving from reactive detection of known illicit actors, to practice identification of strategic financial infrastructure. This requires contextual intelligence, behavioural analysis, infrastructure mapping, and an understanding of how influence and capital intersect digital markets.
All research content and accompanying reports are provided for informational purposes only and should not be relied upon as professional advice. Accessing these materials does not create any professional relationship or duty of care. Readers are encouraged to consult appropriately qualified professionals for guidance. We uphold the highest standards of accuracy in all the information we provide. For any questions or feedback, please contact us at contact@nominis.io.



.jpg)

.png)
