NOMINIS CEO Snir Levi examines the behaviour of recently OFAC-seized wallet addresses, comparing their behaviours to other confirmed Iranian-linked operations. He assesses whether links to Chinese exchange Huobi, temporal analysis, and other indicators may suggest these sanctioned wallets are not actually Iranian at all.
The recent designation involving the freezing of over $340 million in USDT by Tether, alongside action from U.S. authorities, marks one of the most significant crypto enforcement events to date.
While the use of cryptocurrency by the Islamic Revolutionary Guard Corps is well established, this case presents structural and behavioral characteristics that diverge meaningfully from previously observed patterns.
A Departure from Established IRGC Wallet Behavior
Historically, IRGC-linked wallets have demonstrated a consistent operational model:
- Funds are distributed across multiple wallets
- Individual wallet balances are kept relatively low (typically a few million USD)
- Holdings are not retained for extended periods
- Activity is structured to minimize exposure to seizure or freezing mechanisms
This pattern has been observed across prior designations, including networks linked to individuals such as Arash Estaki and Alireza Derakhshan, and the cases of ZedCex and ZedXion exchanges, based in London.
In contrast, the wallets identified in the current designation exhibit markedly different behavior.
Accumulation Followed by Dormancy
On-chain analysis indicates that several of the designated wallets:
- Began operating in mid-2021
- Accumulated large volumes of USDT through repeated high-value transfers
- Became largely inactive from February 2023 onward
Post-2023 activity is minimal, limited to sporadic low-value transactions. This “accumulate-then-freeze” pattern is inconsistent with prior IRGC financial flows, which typically emphasize continuous movement and fragmentation of funds.
Anomalous Exchange Interactions
One notable wallet (TNiq9AXBp9EjUqhDhrwrfvAA8U3GUQZH81) demonstrates irregular interaction with exchange infrastructure:
- Periodic small transfers to wallets associated with Bitfinex
- An inbound transaction of approximately $5 from a Bitfinex-linked user prior to these outflows
This raises key questions around intent and awareness:
- Was this interaction incidental, or indicative of testing behavior?
- Does it reflect indirect exposure of exchange users to sanctioned infrastructure?
Such interaction patterns are atypical for known IRGC-controlled wallets.
Overlap with Fraud Typologies
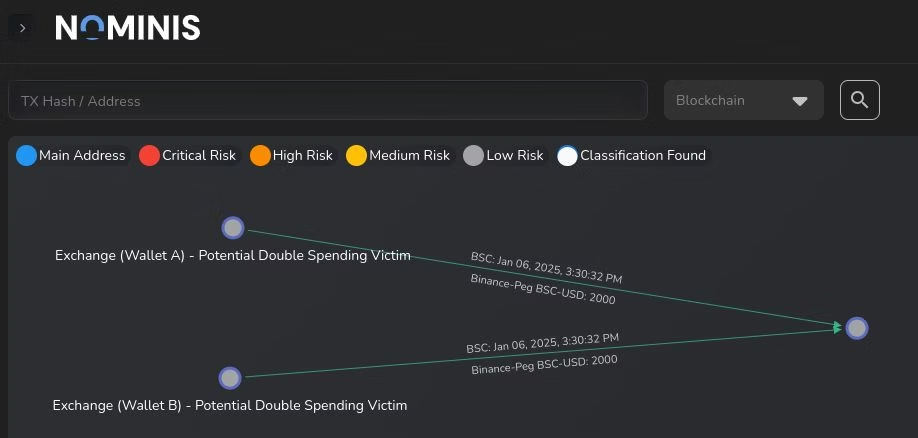
Further analysis shows that this same wallet surfaced in 2025 in connection with a scam-related flow.
This overlap between:
- State-linked financial infrastructure
- Retail-facing fraud activity
introduces additional complexity. It suggests either:
- Reuse of infrastructure across typologies, or
- Unwitting interaction by external actors with compromised or high-risk wallets
Both scenarios carry significant compliance implications.
Network Linkages and Exchange Exposure
Cluster analysis highlights a root wallet (TCXfhTDMuS6pbfCEoACPcBf2EnnhMAAEWh) strongly connected to the broader network.
Tracing flows across this cluster reveals:
- Direct and indirect exposure to platforms such as Huobi (now operating as HTX)
- Linkages to Huione Group infrastructure
- Transaction patterns consistent with historically Chinese-dominated exchange activity (particularly circa 2021)
Additionally, a deposit address associated with HTX (TRX8NbW3gGRyYmDsvkNWjaGgnA74s3ZbRM) received approximately $600,000 linked to entities associated with the Central Bank of Iran. Temporal analysis of this address suggests activity aligned with Asia-based operational cycles.
Key Question: Attribution and Control
The behavioral divergence observed in this case raises a critical question:
To what extent does the frozen $340 million reflect direct IRGC control, versus infrastructure that overlaps with broader, potentially foreign, financial networks?
While attribution remains complex, the data suggests that this network may not conform to previously understood IRGC financial models. Instead, it points toward a more hybridized structure, where state-linked actors, exchange infrastructure, and possibly third-party networks intersect.
Implications for Compliance
This case reinforces several key points for compliance teams:
- Static typologies are no longer sufficient
- Behavioral analysis and clustering are critical for identifying risk
- Exposure to sanctioned networks may occur indirectly through exchange interactions
- Cross-jurisdictional infrastructure adds layers of ambiguity to attribution
Most importantly, it highlights that even well-documented actors such as the IRGC and potentially Chinese state-actors are continuing to evolve their use of blockchain infrastructure.
All research content and accompanying reports are provided for informational purposes only and should not be relied upon as professional advice. Accessing these materials does not create any professional relationship or duty of care. Readers are encouraged to consult appropriately qualified professionals for guidance. We uphold the highest standards of accuracy in all the information we provide. For any questions or feedback, please contact us at contact@nominis.io.