Introduction
TL;DR : NOMINIS February 2026 Key Findings
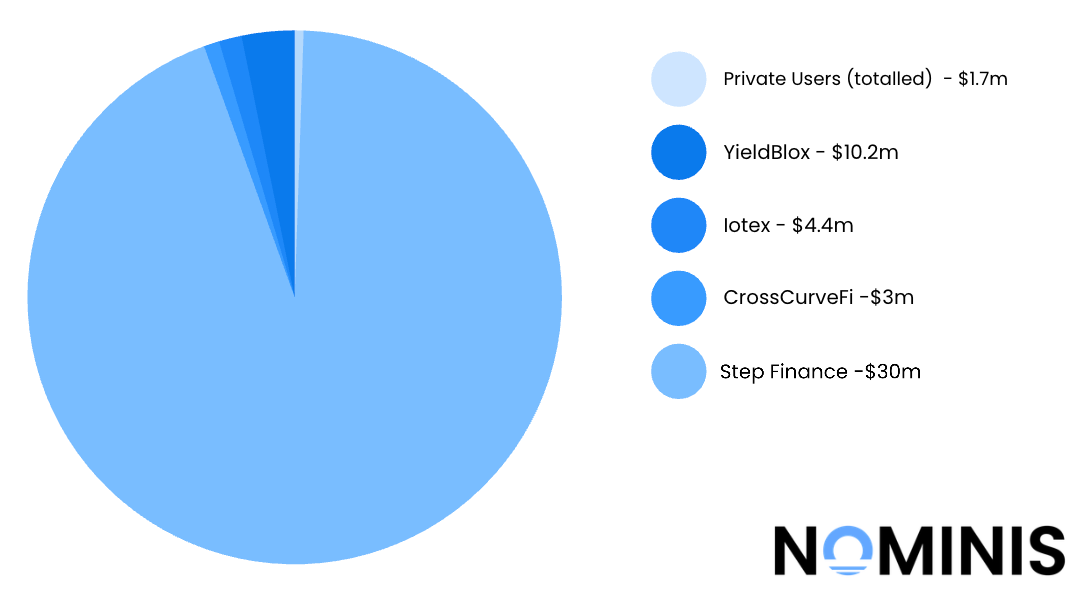
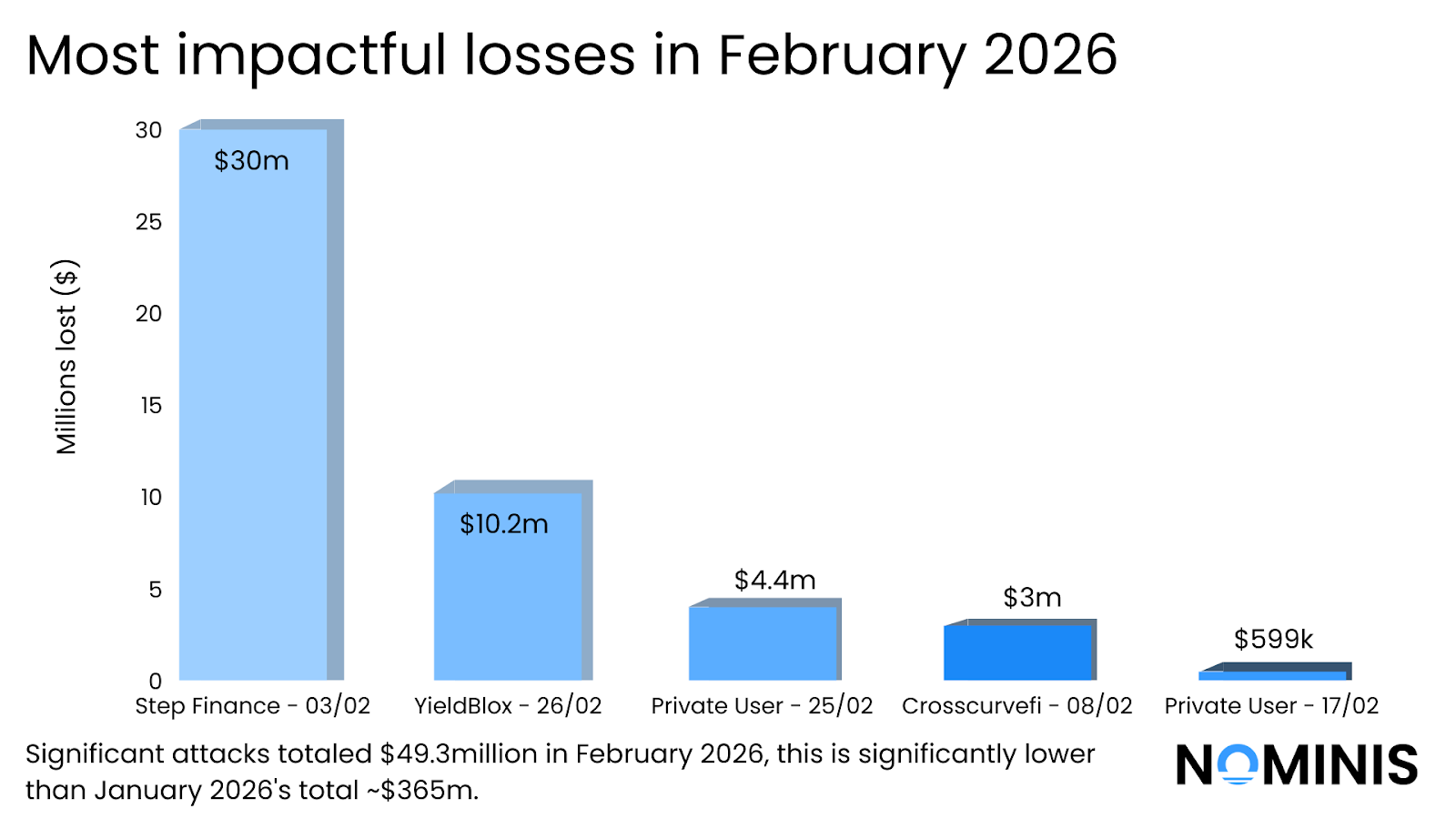
- Approximately $49.3 million was lost across major crypto incidents in February 2026, representing a significant decline compared to the roughly $385 million recorded in January.
- A single infrastructure breach at Step Finance, resulting in approximately $30 million in losses, accounted for more than 60% of the total losses recorded during the month.
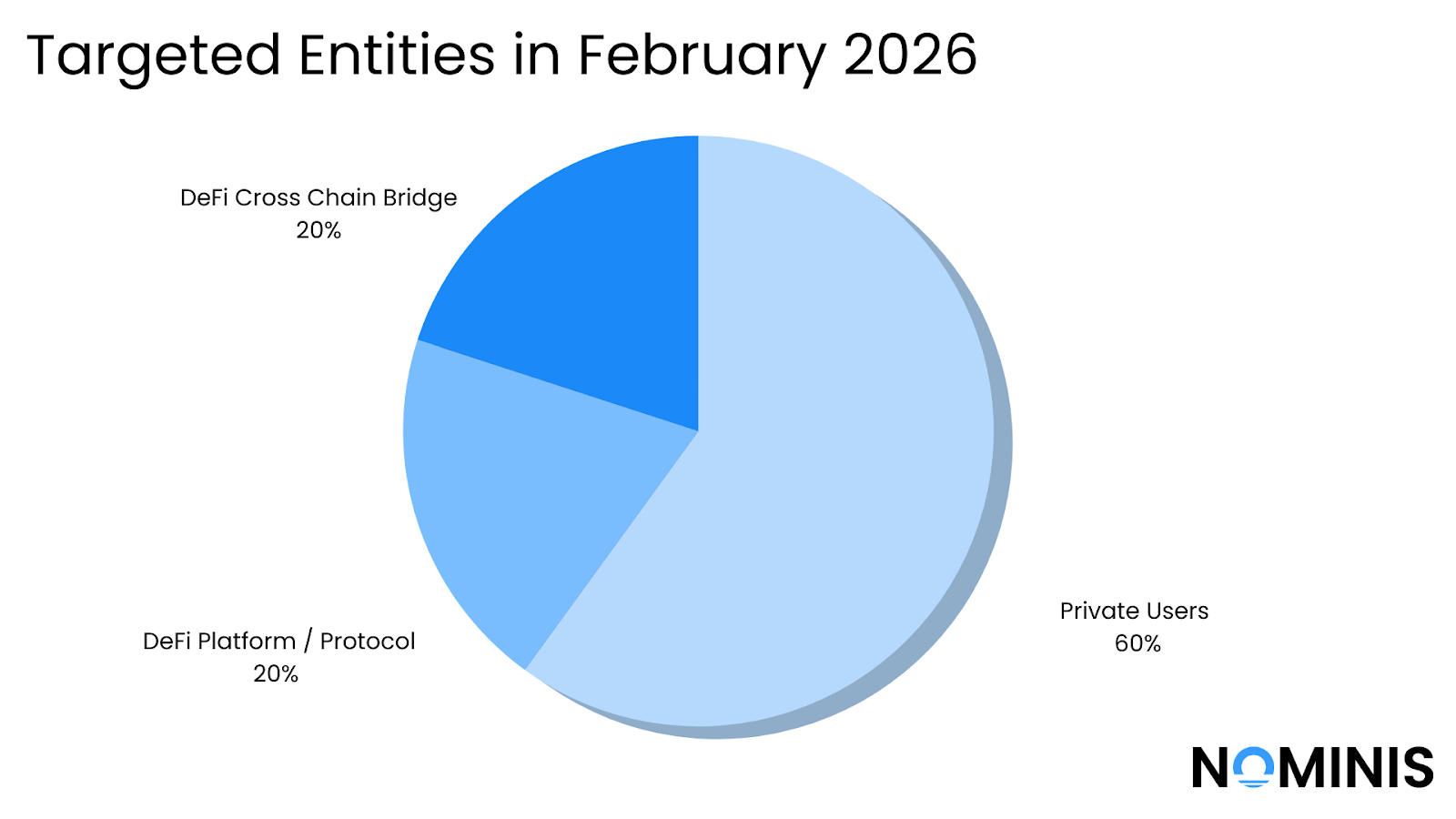
- Private individuals were the most frequently targeted victims, with attackers primarily relying on phishing approvals, malicious signatures, and address poisoning techniques.
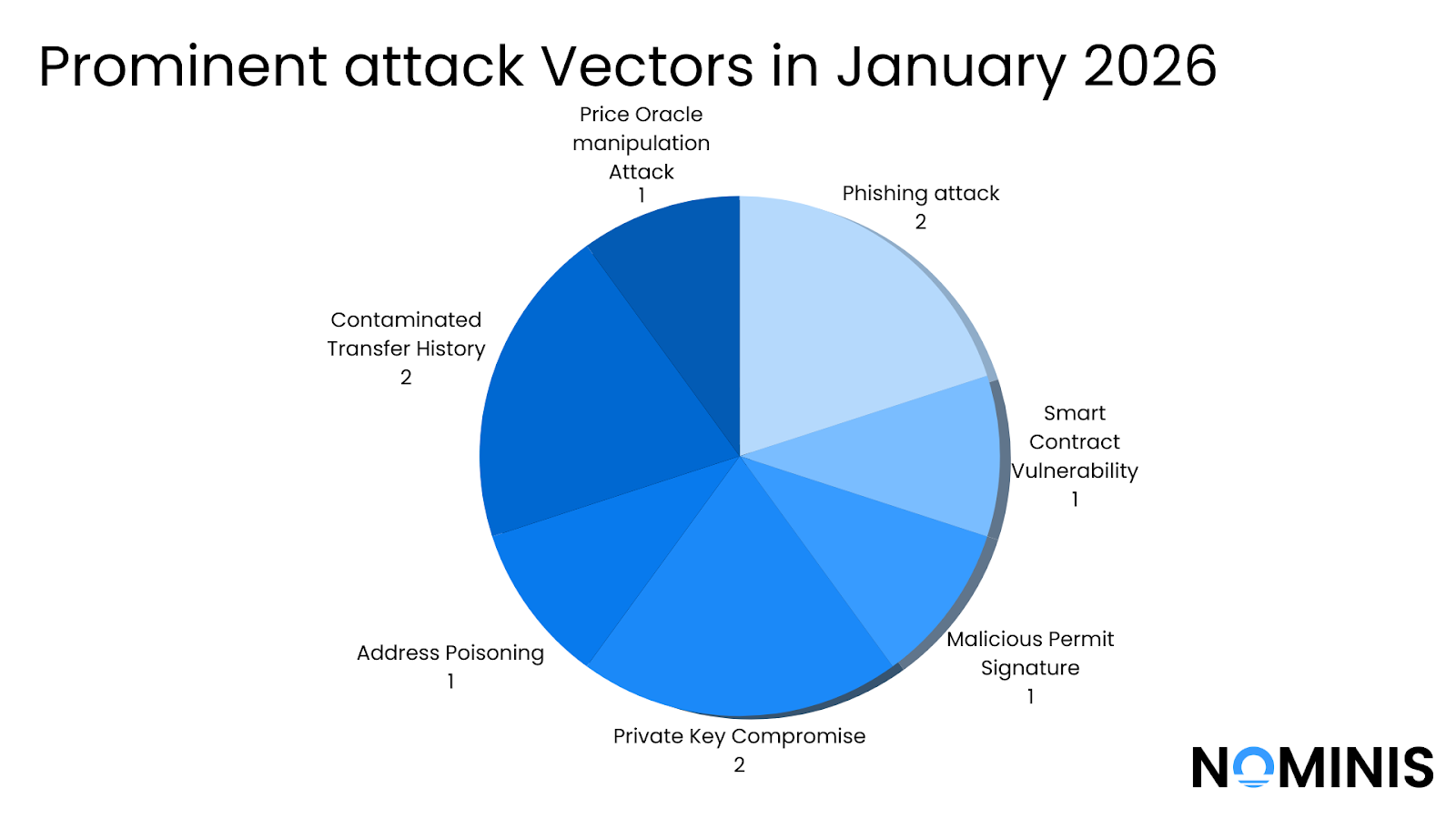
- Authorisation abuse remained the dominant attack vector, as multiple incidents involved victims unknowingly approving transactions that granted attackers permission to transfer funds.
- Across the month, social engineering attacks caused more cumulative damage than technical smart contract exploits, reflecting a continued shift toward attacks that manipulate user behaviour.
- While smart contract vulnerabilities and protocol logic flaws did occur, they generally resulted in smaller financial losses compared to attacks involving compromised permissions or credentials.
- Operational security failures, including private key exposure and seed phrase leaks, continued to create high-impact incidents capable of compromising entire wallets or platforms.
Introduction
February 2026 saw a noticeable decline in the scale of major cryptocurrency security incidents compared to the previous month, with approximately $49.3 million in losses recorded across significant attacks. While this figure is substantially lower than the roughly $385 million reported in January, the incidents that did occur provide important insight into the evolving threat landscape surrounding digital assets.
A single infrastructure compromise accounted for the majority of the month’s losses, demonstrating how breaches involving privileged access or internal operational security failures can rapidly escalate into multi-million-dollar incidents. At the same time, the majority of individual events involved private users falling victim to social engineering attacks, including phishing approvals, malicious transaction signatures, and address poisoning scams.
These patterns reinforce a broader shift that has become increasingly visible across the crypto ecosystem. Rather than relying primarily on complex smart contract exploits, many attackers are focusing on manipulating transaction authorisation and user behaviour, exploiting weaknesses in wallet interfaces, transaction signing prompts, and everyday operational practices.
Alongside direct attacks, February also saw several notable developments affecting the wider crypto security environment, including investigations into phishing infrastructure targeting project administrators, operational security failures leading to large-scale theft, and law enforcement seizures linked to international fraud networks.
Taken together, the events of February highlight that the most significant vulnerabilities in the crypto ecosystem often exist at the intersection of technology, human behaviour, and operational security, rather than within blockchain protocols themselves.
Major Crypto Attacks in February 2026
Private User - 02/02/2026
Type: Contaminated Transfer History
On 2 February, a victim on Ethereum mistakenly sent approximately $100,000 in USDT to a look-alike address after confusing two nearly identical wallet strings. The intended recipient address differed subtly from the actual destination , with only a few middle characters changed, highlighting how address poisoning and near-match scams exploit users who verify only the first and last digits. Typically, to avoid this type of incident, saved contacts or ENS names can be used for known and familiar wallets.
Impact: $100,000
Step Finance - 03/02/2026
Type: Private Key Exposure
A day later, the Solana-based DeFi platform Step Finance reported a major security breach in which attackers were able to access and drain around 261,854 SOL (roughly $27M–$40M) from wallets controlled by the project after compromising devices belonging to its executive team, likely exposing private keys or enabling malicious transaction approvals. The funds were unstaked and transferred out, triggering a massive drop in the price of the native STEP token and forcing Step Finance to halt parts of its platform. Despite recovering about $4.7M in some assets, the financial and operational impact was so severe that the team ultimately announced it would shut down the core platform and affiliated projects like SolanaFloor and Remora Markets, and is planning a buyback for STEP holders based on a pre-hack snapshot. It is likely that the attack itself took place at the end of January, but indicators and investigators were only able to confirm the event at the beginning of February.
Impact: $30,000,000
CrossCurveFi - 08/02/2026
Type: Smart Contract Vulnerability
Towards mid February, the cross-chain bridge protocol CrossCurve suffered a hack that resulted in roughly $3 million in losses across multiple blockchains. The attacker exploited a flaw in the bridge’s smart contract validation logic, specifically in functions responsible for processing cross-chain messages coming from the Axelar network. Because the contract’s access controls were insufficient, the attacker was able to forge malicious cross-chain messages that appeared legitimate to the system. These spoofed messages instructed the protocol’s receiver contract to authorize the release of tokens from its liquidity contracts, effectively unlocking funds without a real deposit on the source chain. After draining assets across several supported chains, the attacker swapped and bridged the stolen tokens into more liquid assets and began laundering them, while the CrossCurve team shut down parts of the protocol to investigate and patch the vulnerability.
Impact: $3,000,000.00
Private User - 10/02/2026
Type:Malicious Permit Signature
Several days later, a phishing style wallet drain was reported, where a user unknowingly signed a malicious increaseAllowance transaction that granted an attacker permission to transfer tokens from their wallet. After the approval was signed, the attacker used that allowance to execute two transfers that drained $118,785 worth of BUSD from the victim’s address. The loss occurred in two transactions (≈23,750 BUSD and ≈95,001 BUSD) sent to scam-associated addresses. The attack did not exploit a protocol or smart contract bug; instead, it relied on social engineering and deceptive transaction prompts that tricked the user into granting token spending permissions.
Impact: $118,785.00
Private User - 17/02/2026
Type: Address Poisoning Scam
A week later, an incident was reported involving an address poisoning scam, which is a local social-engineering technique used to trick users into sending funds to an attacker-controlled wallet. In this case, the attacker sends a small ‘dust’ transaction to the victim’s wallet using an address that visually resembled a legitimate address the victim had previously interacted with. When the victim later attempted to copy a past transaction from their wallet history, they mistakenly copied the attacker’s look-alike address instead of the legitimate one and sent funds to it.
Impact: $599,714.00
Private User - 18/02/2026
Type: Phishing Approval Signature
The following day, another incident was reported, where a victim unknowingly authorized a malicious token allowance that allowed the attacker to drain funds from their wallet. The victim address 0x9940…d5c2 signed a transaction calling approve(address,uint256) on the USDT (Tether) contract. This approval granted a scammer-controlled address permission to spend the victim’s tokens. Shortly after the approval was confirmed on-chain, the attacker used the granted allowance to execute transferFrom() transactions, moving approximately $337,069 in USDT from the victim’s wallet to scam-associated addresses.
Impact: $337,069.00
Private User - 18/02/2026
Type: Contaminated transfer history
The same day, an address poisoning scam took place, in which a victim mistakenly sent approximately $157,000 to a scammer-controlled wallet after copying an address from their contaminated transaction history. The attacker previously inserted a look-alike address into the victim’s history that closely resembled the legitimate destination. When the victim attempted to send funds and copied the address, they accidentally selected the malicious address 0xa7A00BD2…03F0 instead of the intended address 0xa7a9c35a…03F0, resulting in the transfer of funds to the attacker. The technique exploits the fact that many wallet interfaces truncate addresses, making visually similar addresses difficult to distinguish.
Impact: $157,000.00
Iotex - 24/02/2026
Type: Private Key Compromise
Several days later, the IoTeX ecosystem suffered a security incident in which attackers exploited a vulnerability affecting a third-party liquidity and bridge infrastructure connected to the IoTeX network, allowing them to mint and withdraw tokens that were not properly backed by locked assets. The exploit centered on flaws in the cross-chain minting and validation logic, enabling the attacker to manipulate the system so that tokens were issued without the corresponding collateral being secured on the source chain. Once minted, the attacker quickly swapped and moved the assets across the ecosystem to extract value before the issue was detected and mitigated.
Impact: $4,400,000.00
Private User - 25/02/2026
Type: Phishing Approval Signature
The following day an incident was reported by Scam Sniffer involving a phishing approval attack in which a user was tricked into signing a malicious transaction that granted a scammer permission to spend tokens from their wallet. After the victim signed the approval, the attacker immediately used the granted allowance to execute transferFrom() transactions, draining the tokens from the wallet and moving them to scam-associated addresses. The attack did not involve a smart contract exploit or private key compromise; instead, it relied on the victim unknowingly authorizing token access through a deceptive signing prompt.
Impact: $388,051.00
YieldBlox Hack - 26/02/2026
Type: Phishing Approval Signature
Towards the end of the month, the YieldBlox protocol, a DeFi lending and borrowing platform, suffered an exploit that allowed an attacker to manipulate the protocol’s pricing and collateral logic to extract funds. By exploiting weaknesses in how the protocol calculated asset values and collateral requirements, the attacker was able to borrow against manipulated collateral positions and withdraw assets beyond what should have been permitted. Once the exploit was executed, the attacker rapidly moved the funds out of the protocol and swapped them into more liquid assets to obscure the trail.
Impact: $10,200,000
Significant Events in February 2026
February 2026 saw several notable incidents across the cryptocurrency ecosystem, ranging from sophisticated social engineering attacks to large-scale enforcement actions and operational security failures. Together, these events highlight how vulnerabilities in human behaviour, infrastructure design, and operational practices continue to play a major role in crypto-related security incidents.
One of the most significant technical investigations published during the month came from SlowMist, which detailed a token vesting phishing-poisoning campaign targeting crypto project teams. The attackers created malicious interfaces that imitated legitimate vesting or token management tools used by project administrators. By tricking operators into interacting with these interfaces, the attackers were able to modify contract permissions and redirect token allocations. The campaign demonstrates how phishing in the crypto ecosystem increasingly targets administrative infrastructure rather than retail users, allowing attackers to manipulate token distribution mechanisms and access high-value treasury assets.
February also saw a major operational security failure involving the South Korean National Tax Service. Authorities began investigating how a seed phrase was inadvertently exposed in a publicly shared photograph, allowing attackers to reconstruct the wallet and steal approximately $4.8 million in cryptocurrency. The case illustrates how even well-secured wallets can be compromised when sensitive information is exposed through everyday operational practices such as photographs, screenshots, or documentation.
Institutional infrastructure was also affected. Security firm Halborn published an analysis of the Figure Technology breach, in which attackers targeted systems associated with the blockchain-based financial services platform. The investigation suggested that attackers were able to exploit weaknesses in internal infrastructure and access sensitive systems connected to digital asset operations. The incident highlighted the risks faced by fintech platforms operating at the intersection of traditional finance and blockchain infrastructure.
At the same time, law enforcement continued to demonstrate its ability to track and recover illicit funds. The U.S. Department of Justice announced the seizure of approximately $6.1 million in cryptocurrency linked to a global investment fraud scheme commonly known as “pig-butchering.” Investigators traced the funds across blockchain transactions and were able to identify wallets associated with the criminal network, ultimately securing the seizure through legal forfeiture processes. The case illustrates the increasing sophistication of blockchain tracing techniques used by investigators to disrupt organized fraud operations.
Taken together, these incidents demonstrate the evolving threat landscape surrounding digital assets. While blockchain technology itself remains transparent and traceable, attackers continue to exploit weaknesses at the edges of the ecosystem, through social engineering, operational mistakes, compromised interfaces, and fraudulent investment schemes. February’s events reinforce the importance of combining on-chain analytics, operational security practices, and intelligence-driven compliance tools to detect and prevent these types of threats.
NOMINIS Unique Findings:
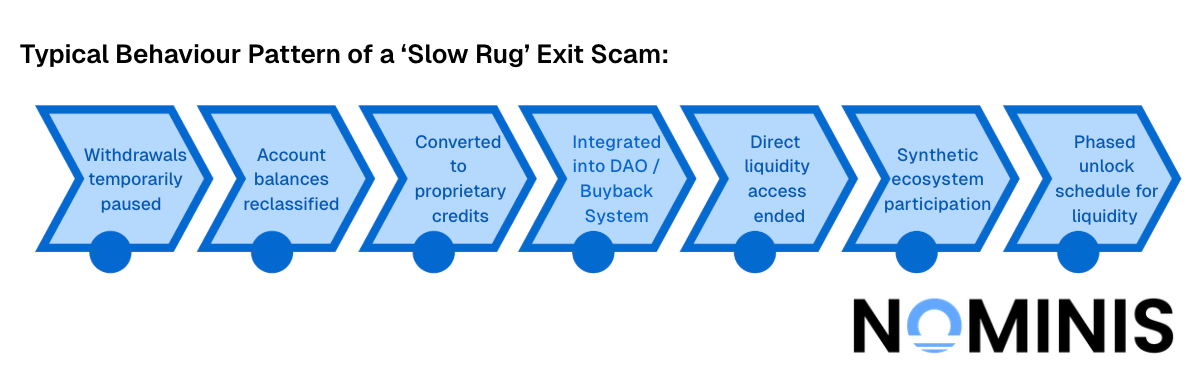
Following NOMINIS investigation into suspicious behaviour, mining platform BitHarvest.io was reported, with cloudflare preventing access to the site. NOMINIS recognised that the platform had entered the exit phase of a slow rug scam, in which user’s funds will be converted into ‘Wallet Credits’ which were ‘non transferable’, as a solution to ‘technical constraints’ that the platform was experiencing.
More information about the investigation can be found here.
Meanwhile, NOMINIS also investigated the potential risk to national security posed by betting platform Polymarket. Recognising a pattern of insider trading, NOMINIS research identified the behaviour patterns of certain users who appeared to have insider information, betting too confidently, far too in advance, and identified other users whose behavior follows the same pattern.
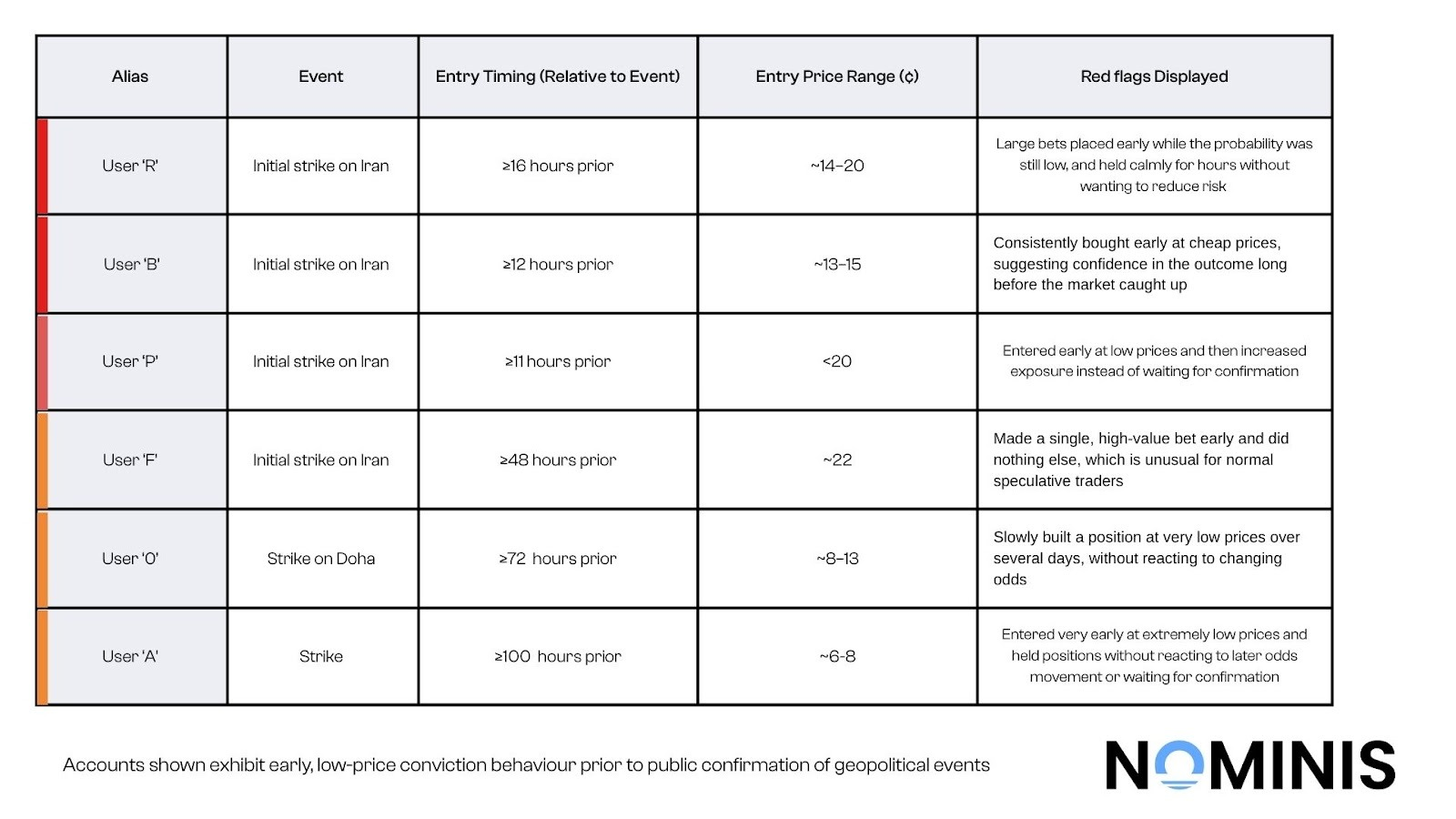
This investigation can be found here.
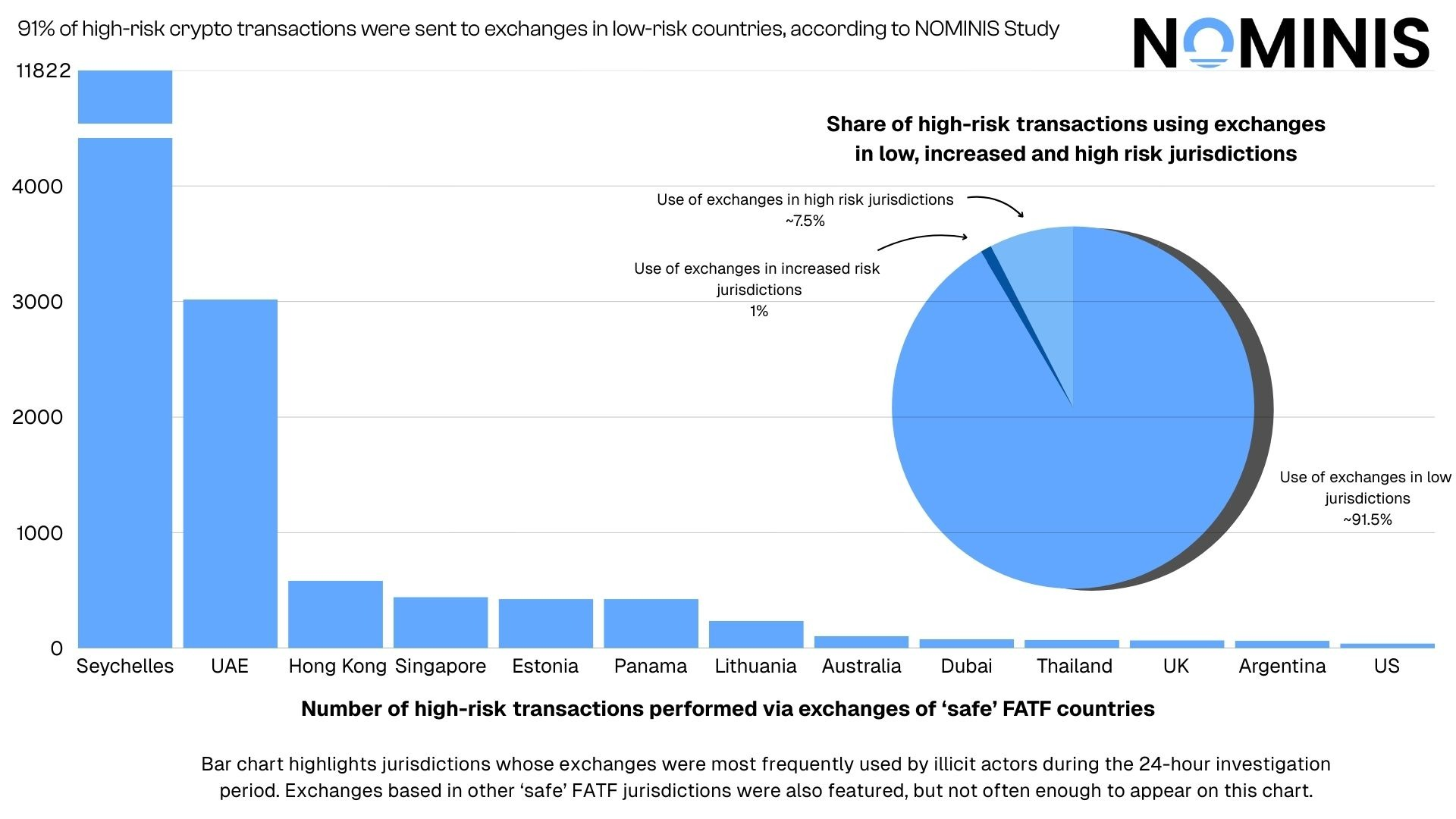
Finally, NOMINIS released a report with analysis finding that terrorist-linked crypto transactions are 12 times more likely to flow through exchanges located in countries classified as “low risk” by the Financial Action Task Force (FATF) than through exchanges in high-risk jurisdictions. Rather than operating primarily in weak regulatory environments, many terror-financing networks appear to deliberately route funds through platforms in well-regulated countries, likely to benefit from the liquidity, stability, and reputational cover associated with those markets.
The findings challenge a common compliance assumption that high-risk jurisdictions represent the primary exposure for terror financing. In practice, illicit actors often move funds through multiple intermediaries and reputable exchanges, creating distance between the origin of funds and their final destination. This layered transaction behavior allows terrorist organizations to access the global crypto economy while blending into normal trading activity.
The report concludes that effective crypto compliance cannot rely solely on jurisdiction-based risk scoring. Instead, exchanges and financial institutions must apply transaction-level monitoring and behavioral analysis, as illicit actors increasingly exploit trusted infrastructure in lower-risk FATF jurisdictions to move and obscure funds.
The report in full can be found here.
Interesting data shared exclusively with NOMINIS by Lionsgate Network corroborate with NOMINIS data exploring crypto scams in February 2026.
Lionsgate Network received 180 reported client inquiries this month, with victims having collectively lost approximately $45 million to fraud schemes. The average loss per victim was around $250,000, while the largest individual case reached $6.1 million, highlighting the significant financial impact that a single successful operation can generate. Victims most commonly fell within the 45- 70 age range and frequently included medical professionals, technology sector employees, and retirees: individuals with high available liquidity and a strong baseline level of trust, traits that make them particularly vulnerable to socially engineered investment scams.
The majority of such cases involved pig butchering schemes, in which attackers build long-term online relationships before introducing fraudulent crypto investment opportunities. Fake trading platforms accounted for roughly 15% of cases, while job-related scams represented around 7%.
According to Founder and CEO, Bezalel Eithan Raviv, social media is heavily relied upon and is becoming the primary entry point for such financial crimes. On the topic, he shared
‘In the age of AI, financial fraud is no longer just a cybersecurity issue. It is a behavioral attack. If you can manipulate the person, you no longer need to hack the system.’
NOMINIS Updates:
February 2026 saw the launch of a new feature on the platform, the NOMINIS forensic tool. This investigative capability combines our intelligence from our database concerning wallets in the network, while visualizing the flow of funds between wallets. For law enforcement agencies, private investigators, and coin recovery companies, this tool provides a demonstration of all the data provided in the address exposure tool, while exploring the flow of funds between wallets.
This month also saw introductions of new security features for existing users subscribed to the NOMINIS platform. NOMINIS has increased our security functions to reflect our dedication to our clients for secure and easy use of our platform.
Concluding Insights:
The incidents recorded in February 2026 reinforce a growing trend in the crypto ecosystem; many of the most damaging attacks rely on exploiting human behaviour and transaction authorisation rather than complex technical vulnerabilities.
Although total losses declined significantly compared to January, the concentration of more than 60% of the month’s losses in a single infrastructure breach highlights how privileged access failures and operational security weaknesses can rapidly escalate into major financial incidents. At the same time, the majority of individual attacks targeted private users through phishing approvals, malicious signatures, and address poisoning scams.
Together, February’s events demonstrate that the most critical vulnerabilities often exist at the intersection of technology, operational practices, and user behaviour. Preventing future losses will require not only secure protocols, but also stronger monitoring, intelligence-driven investigations, and better safeguards around transaction approvals and wallet security.
All research content and accompanying reports are provided for informational purposes only and should not be relied upon as professional advice. Accessing these materials does not create any professional relationship or duty of care. Readers are encouraged to consult appropriately qualified professionals for guidance. We uphold the highest standards of accuracy in all the information we provide. For any questions or feedback, please contact us at contact@nominis.io.


