TLDR
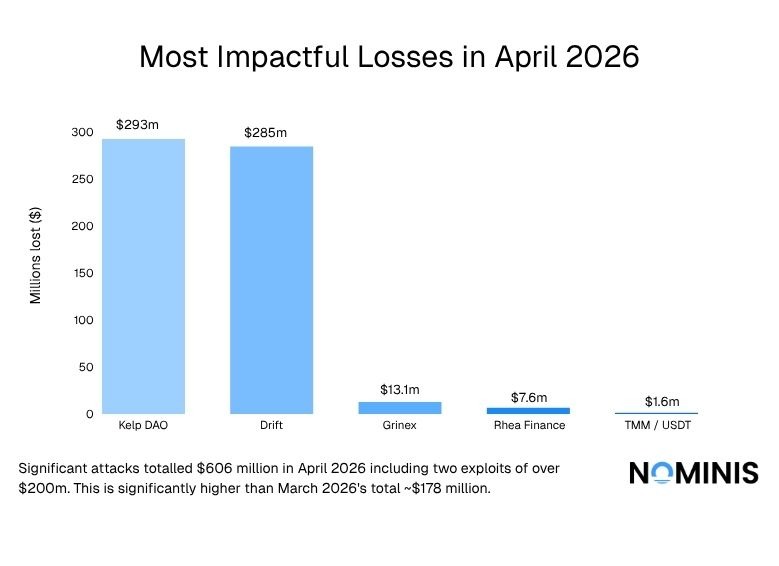
- Total losses reached approximately $606.7 million, a sharp increase from $178.1 million in March 2026 (more than threefold growth month-on-month)
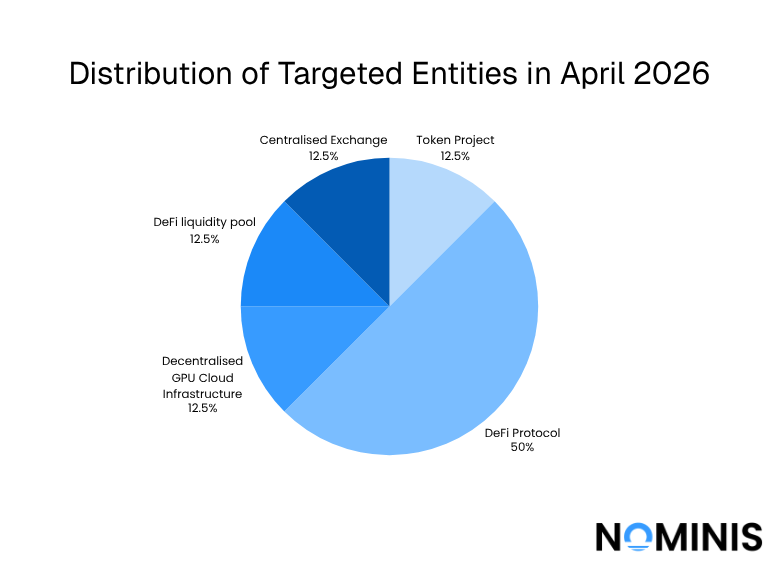
- DeFi protocols were the most targeted entities
- 5 out of 8 incidents
- Responsible for nearly all financial losses
- Losses were highly concentrated in two incidents:
- Kelp DAO: ~$293M
- Drift: ~$285M
- Combined total: ~$578M (~95% of all losses in April)
- Most financially damaging attack vector: oracle manipulation:
- Drove the largest exploits of the month
- Remains a critical structural weakness in DeFi systems
- Other attack vectors observed:
- Flash loan attacks
- Liquidity exhaustion
- Cross-chain bridge exploits
- Access control failures
- Admin key compromise (e.g. Wasabi Protocol)
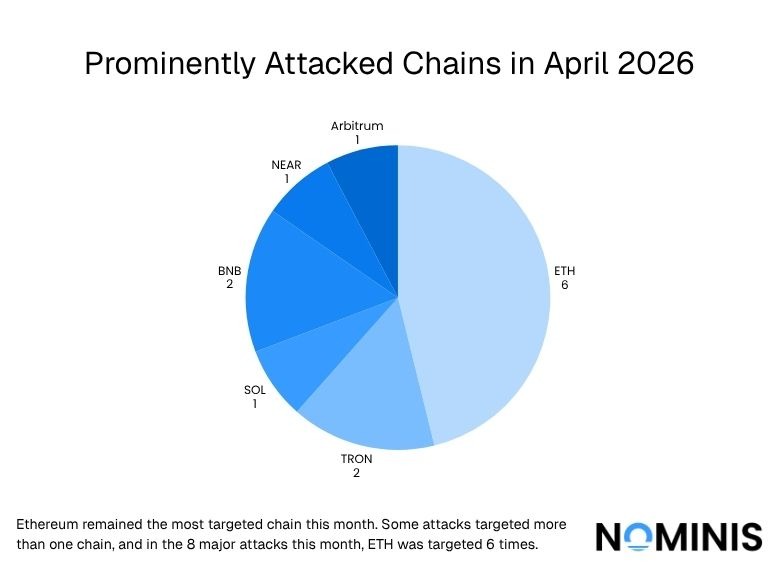
- Most targeted blockchain ecosystem:
- Ethereum was involved in the majority of incidents
- Layer 2 networks such as Arbitrum were also affected
- Most targeted assets:
- USDT, USDC, and ETH
- High-liquidity tokens were consistently targeted due to ease of transfer and liquidation
- Non-DeFi entities experienced different attack patterns:
- Grinex lost ~$13.1M
Introduction:
April 2026 marked a sharp escalation in both the scale and impact of crypto-related security incidents, with total recorded losses rising dramatically compared to the previous month. A combination of high-value DeFi exploits, infrastructure weaknesses, and emerging attack vectors contributed to one of the most financially significant periods of the year so far. While March already highlighted persistent vulnerabilities across the ecosystem, April demonstrated how quickly losses can compound when large, liquidity-rich protocols are compromised.
The month was defined not only by the volume of attacks, but by their concentration, where a small number of incidents accounted for the overwhelming majority of funds lost. At the same time, attackers continued to diversify their methods, targeting everything from oracle mechanisms and liquidity pools to cross-chain infrastructure and centralized credentials. Beyond direct financial theft, parallel incidents affecting technology platforms also underscored the growing importance of supply-chain security and the broader attack surface surrounding crypto and AI-integrated systems.
Major Crypto attacks in April 2026
#LML - 01/04/2026
Type: Liquidity Exhaustion
To begin the month, the #LML project experienced a significant exploit on its chain, resulting in a loss of almost a million dollars. The attacker drained funds denominated in USDT, subsequently swapping it into ETH before routing the assets through Tornado Cash to obfuscate transaction trails. The incident triggered a severe market reaction with the LML token collapsing 99.6% in value.
Impact: $950,000.00
Drift - 01/04/2026
Type: Hybrid attack: Oracle Manipulation & Multisig Compromise
The same day, Drift Protocol on Solana experienced a significant hybrid exploit, resulting in major losses. The Attacker introduced and manipulated a malicious collateral asset, using it to extract real funds denominated in USDC and Solana, while leveraging compromised governance approvals to enable withdrawals. A portion of the stolen assets was subsequently bridged to Ethereum and converted into Ethereum, indicating cross-chain laundering activity.
Impact: $285,000,000.00
AethirOFTAdapter - 10/04/2026
Type: Cross-chain Bridge Exploit
10 days later, the Aethir protocol experienced a cross-chain bridge exploit affecting its ATH token infrastructure. The attack targeted bridge contracts connecting Ethereum to other chains, specifically exploiting the AethirOFTAdapter to drain funds before they were bridged from BNB Chain to Tron. The attacker leveraged a smart contract vulnerability in the cross-chain messaging or bridging logic, enabling unauthorized transfers of assets. Upon detection, Aethir promptly disabled the compromised contracts and coordinated with exchanges to blacklist attacker wallets, limiting further losses. Notably, the primary ATH token supply on Ethereum remained unaffected.
Impact: $400,000.00
TMM / USDT - 13/04/2026
Type: Flash Loan incident
In the middle of the month, the TMM protocol on BNB Chain experienced a flash loan-driven exploit targeting its liquidity pools, resulting in losses of approximately $1.6M. The attacker leveraged large flash loans to manipulate the reserves of the TMM/USDT pair, artificially distorting pricing by burning TMM tokens and creating an imbalance in the pool. This enabled the extraction of an outsized amount of USDT before the system could rebalance.
Impact: $1,665,000.00
Rhea Finance - 16/04/2026
Type: Oracle Manipulation Attack
Several days later, Rhea Finance on NEAR Protocol experienced a critical exploit driven by oracle manipulation and fake collateral abuse. The attacker deployed malicious tokens and created artificial liquidity conditions to generate fabricated price data, which was then accepted by the protocol’s pricing mechanisms. Using these inflated assets as collateral, the attacker was able to borrow and drain real funds from the platform, leaving it exposed to worthless tokens.
Impact: $7,600,000.00
Grinex - 17/04/2026
Type: (Likely) Access Control Failure
The following day, Grinex Exchange, a Russian-linked entity, suffered a cyberattack that resulted in the theft of approximately $13 million (1 billion roubles), forcing the platform to suspend operations. The breach targeted centralized exchange infrastructure, leading to the unauthorized withdrawal of user-held assets, including funds linked to its ecosystem such as the A7A5 stablecoin.
While the exact attack vector was not disclosed, the incident is consistent with a centralized exchange wallet compromise rather than a smart contract exploit. The attack prompted immediate shutdown measures and raised concerns around custodial risk, particularly given the platform’s role in facilitating cross-border crypto flows under sanctions pressure.
Impact: $13,100,000.00
Kelp DAO - 18/04/2026
Type: Oracle Manipulation Attack
Following the Grinex hack, Kelp DAO, a liquid restaking protocol on Ethereum, experienced a targeted economic exploit involving its rsETH token. The attacker manipulated pricing and share accounting mechanisms tied to Ethereum and rsETH, enabling them to mint or redeem assets at artificially favorable rates and extract value from the protocol. The incident highlights weaknesses in valuation logic within restaking systems.
Impact: $293,000,000.00
Wasabi Protocol - 30/04/2026
Type: Admin Key Compromise
At the end of the month, Wasabi protocol experienced an admin key compromise, where attackers gained control of the protocol’s deployer (admin) private key and used it to drain funds. Once they had this key, they were able to grant themselves full administrative privileges and upgrade core smart contracts, such as vaults and liquidity pools, to malicious versions that siphoned assets to attacker-controlled wallets. This allowed them to steal roughly $5 million across multiple blockchains without exploiting a traditional coding bug. Instead, the attack took advantage of Wasabi’s reliance on a single admin key with no protections like multisig or timelocks.
Impact: $5,000,000
Concluding Thoughts
Overall, the April 2026 data reinforces the continued dominance of DeFi protocols as the primary target for attackers, accounting for half of all recorded incidents and the vast majority of financial losses.
While March 2026 saw approximately $178.1 million stolen across major crypto incidents, April’s losses were significantly higher and heavily concentrated in a small number of large-scale exploits. April’s total losses saw about $606,715,000.
In particular, the attacks on Kelp DAO and Drift alone accounted for the overwhelming share of funds lost, highlighting how a few high-impact breaches can distort monthly totals and emphasizing the systemic risk within large DeFi platforms.
From an attack vector perspective, oracle manipulation proved to be the most financially damaging method, responsible for multiple high-value exploits during the month. However, the diversity of attack types, including flash loan attacks, liquidity exhaustion, cross-chain bridge exploits, and access control failures, demonstrates that there is no single point of failure across the ecosystem. A notable case is Wasabi Protocol, where an admin key compromise enabled attackers to bypass smart contract vulnerabilities entirely and take direct control of funds. This highlights the persistent risk of centralized control mechanisms within otherwise decentralized systems.
In terms of infrastructure, the Ethereum ecosystem remained the most targeted, reflecting its position as the largest hub for DeFi activity and liquidity. Correspondingly, attackers consistently focused on high-liquidity tokens, particularly USDT, USDC, and ETH, which offer ease of movement and liquidation across chains.
In conclusion, April’s incidents highlight three key trends: the continued concentration of risk in DeFi protocols, the outsized impact of oracle and privileged-access exploits, and the strategic targeting of high-liquidity ecosystems and assets. Together, these patterns suggest that while attack techniques are evolving, the fundamental drivers, access to liquidity, control over critical infrastructure, and weaknesses in governance, remain consistent.
All research content and accompanying reports are provided for informational purposes only and should not be relied upon as professional advice. Accessing these materials does not create any professional relationship or duty of care. Readers are encouraged to consult appropriately qualified professionals for guidance. We uphold the highest standards of accuracy in all the information we provide. For any questions or feedback, please contact us at contact@nominis.io.


